In This Article
- What Agent 365 Changes for Financial Institutions
- The Five Governance Controls You Need Before May 1
- The Regulatory Timeline You Cannot Ignore
- Default vs. Governed: What Happens Without Preparation
- Sub-Processor Relationships and Data Protection
- How Guardian Builds the Governance Foundation
- Frequently Asked Questions
Microsoft Agent 365 goes generally available on May 1, 2026. Bundled into the new M365 E7 Frontier Suite at $99 per user per month, it gives autonomous AI agents their own identities, permissions, and decision-making authority inside your Microsoft 365 tenant. For credit unions, community banks, and mortgage companies, this is not a product demo to schedule later. It is a governance decision that needs answers now.
Agent 365 is the governance framework for managing AI agents across your M365 environment. It provides Entra Agent IDs, lifecycle controls, and audit trails that bring structure to autonomous AI operations. Copilot Studio builds the agents. Copilot Cowork, launched March 30, 2026 on Anthropic's Claude technology platform, runs multi-step tasks in the background. Agent 365 is what keeps all of it accountable.
The distinction matters because agents are not Copilot prompts. They act on behalf of users, inherit permissions, access sensitive data, and make decisions without real-time human oversight. Microsoft's Wave 3 announcement on March 9, 2026 made this shift explicit: AI in M365 is moving from assistant to operator. Financial institutions that treat this like another feature rollout will find themselves explaining agent actions to examiners with no audit trail to reference.
Short on time? Autonomous AI, your data, and the 30-second version.
Agents don't stop to ask permission, and once they're embedded in a Copilot workflow, the blast radius of one ungoverned prompt is the entire tenant. The Short frames the risk in 30 seconds; the article shows how Agent 365 observes, governs, and secures every agent before it talks to a customer record.
Subscribe & View ChannelWhat Agent 365 Changes for Financial Institutions
Until now, AI in M365 was conversational. You asked Copilot a question, it answered, you decided what to do. Agent 365 changes that model. Agents operate autonomously: they process loan documents, respond to compliance queries, execute workflows across applications, and take actions that used to require a human clicking through screens.
Microsoft built Agent 365 around three core capabilities that directly affect how financial institutions manage risk:
Entra Agent ID
Every AI agent receives a unique Microsoft Entra identity, separate from the user who created it. This identity carries its own permissions, access boundaries, and audit history. Examiners can trace exactly what an agent did and why.
Agent Registry
A centralized inventory in the M365 Admin Center tracking all agents across your tenant. No more guessing which department built what agent or what data it can access. The registry shows agent owners, status, and scope.
Lifecycle Controls
Agents follow a governed lifecycle from creation through retirement. Approval workflows gate deployment. Activity monitoring flags anomalies. Decommissioning procedures ensure agents do not persist after their purpose ends.
For enterprise clients already on E5, the path is straightforward. E7 adds Agent 365 ($15 standalone), Copilot ($30 standalone), and the Entra Suite ($12 standalone) for a total of $99 per user per month. The $9 upgrade from E5 makes this the simplest upsell conversation in the M365 portfolio.
For most ABT clients, those credit unions and community banks with 50 to 300 employees on Business Premium, the agent governance conversation comes later. The immediate priority is securing the tenant with Guardian and deploying Copilot Business at $32 per user per month (promotional pricing through June 30, 2026). Agent 365 enters the picture at Rung 5 of the Copilot Adoption Ladder, after Copilot Business and Purview are operational.
Is Your Tenant Ready for AI Agents?
ABT's AI Readiness Scan evaluates your governance foundation before autonomous agents go live.
The Five Governance Controls You Need Before May 1
Agent 365 provides the framework. Your institution provides the policies. Without explicit governance controls configured before agents go live, every agent inherits default permissions that were designed for human users, not autonomous AI operating across your tenant at machine speed.
These five controls form the governance foundation that separates a prepared institution from one reacting to its first agent-related incident:
Assign unique Entra identities to each agent with scoped permissions. No agent should inherit a user's full access. Define what data each agent can read, which systems it can modify, and what actions require escalation.
Set explicit boundaries on what information agents can access and process. Sensitivity labels, DLP policies, and Purview classifications become the guardrails that prevent agents from surfacing restricted data in automated workflows.
Establish approval workflows for agent creation, modification, and retirement. Every agent should have an owner, a defined purpose, a review schedule, and a decommissioning plan. Orphaned agents with active permissions are audit findings waiting to happen.
Configure logging that captures agent decisions, data access patterns, and action outcomes. When an examiner asks what your compliance agent did with member financial data last Tuesday, the answer needs to be specific and documented.
Define which agent actions require human review before execution. Financial transactions, regulatory submissions, member communications, and any action with material consequences should have a human in the loop, at least during the initial deployment phase.
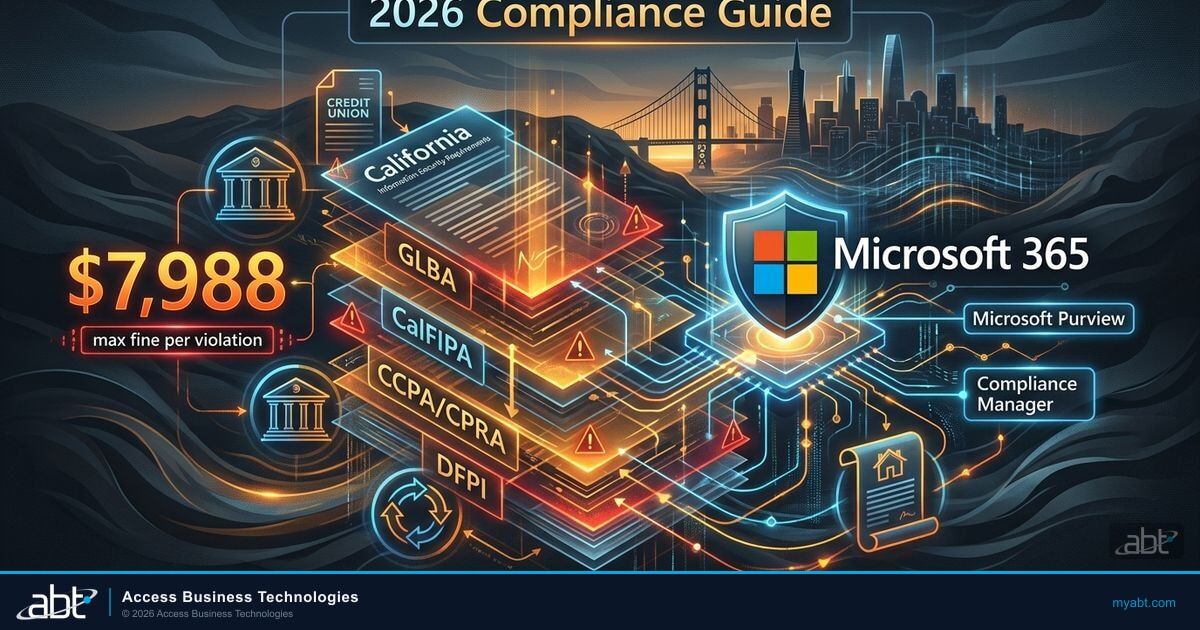
The five controls are not optional extras. The Treasury Department's Financial Services AI Risk Management Framework, published February 2026, lays out 230 control objectives for AI in financial services. Developed with the Cyber Risk Institute and more than 100 financial institutions, it treats agent governance as a baseline expectation, not an aspirational goal. Institutions deploying Agent 365 without these controls will find themselves out of alignment with the framework their examiners are already referencing.
The Regulatory Timeline You Cannot Ignore
Agent 365's May 1 launch date does not exist in isolation. It lands in the middle of a regulatory and licensing calendar that compounds the governance pressure on financial institutions:
Why the Timeline Matters for Financial Institutions
Each date on this timeline adds governance requirements. The Anthropic sub-processor relationship means your vendor risk management program needs updating. The Treasury framework gives examiners specific controls to check. Colorado AI Act applies to any FI with Colorado customers. And Agent 365 makes all of this operational, not theoretical, on May 1.
Default vs. Governed: What Happens Without Preparation
The gap between a default Agent 365 deployment and a governed one determines whether your institution controls its AI agents or explains their behavior after the fact.

Agents inherit user permissions. No approval gates on agent creation. Activity logs exist but are not configured for compliance review. Data boundaries follow existing SharePoint permissions, which most FIs have not audited for agent-appropriate access. Result: agents operate with the same access as the employee who built them, across every document library and mailbox that employee can reach.
Agents receive scoped Entra identities with least-privilege access. Approval workflows gate creation and modification. Audit logs feed into compliance dashboards. Data boundaries are explicitly defined through sensitivity labels and DLP policies. Human approval gates intercept high-risk actions before execution. Result: every agent action is traceable, bounded, and reviewable.
Most financial institutions already have the licensing foundation for governed AI. Microsoft states that all Copilot data remains within the Microsoft 365 service boundary, protected by Enterprise Data Protection. Prompts and responses are never used to train foundation models. But these baseline protections address data privacy, not agent governance. Your Copilot data stays private. Your agents still need explicit rules about what they can do with that data.
Sub-Processor Relationships and Data Protection
The multi-model reality of M365 Copilot adds a layer that financial institutions need to address in their vendor risk management programs. Since January 7, 2026, Anthropic is a designated sub-processor for M365 organizations using Copilot with Claude models.
What This Means for Your Vendor Risk Program
The Anthropic sub-processor relationship falls under OCC Bulletin 2023-17, the interagency guidance on third-party relationships and risk management published June 6, 2023. Your institution's vendor management program needs to document this sub-processor relationship, assess the data flows, and update your risk register. This is not optional for institutions subject to OCC, FDIC, or NCUA examination.
Copilot Cowork, the background agent execution capability launched March 30, 2026, runs on Claude's reasoning engine. The Researcher feature uses GPT to draft research reports and Claude to critique them for accuracy, scoring 13.8% higher on Microsoft's DRACO accuracy benchmark than single-model approaches. This multi-model architecture means your institution's data touches multiple AI systems, each with its own processing characteristics, even though all processing stays within Microsoft's service boundary.
For institutions evaluating agentic AI governance frameworks, the sub-processor question extends to Agent 365. Agents built in Copilot Studio may use different models depending on the task. Your governance framework needs to account for which models process which data, and your audit documentation needs to reflect that reality.
Agent 365 at $15 per user per month is the governance plane OCC Bulletin 2023-17 expects.
Copilot CoWork is rolling out through Frontier Early Access, and the Claude-based agents inside it are third-party relationships under OCC Bulletin 2023-17. The long-form video maps five governance controls -- DLP for agents, conditional access for agent identities, sensitivity-label inheritance, Purview audit logging, and an AUP for autonomous AI -- to Agent 365's observe, govern, and secure pillars. Watch it before you let your first agent touch production data.
ABT Partner Insight | Tier 1 Cloud Solution Provider (CSP)
As a Tier-1 CSP managing M365 tenants for 750+ financial institutions, ABT tracks every Microsoft licensing change, sub-processor update, and compliance requirement as it affects regulated environments. The Agent 365 rollout requires coordination between licensing, identity management, data governance, and compliance documentation. Institutions that treat these as separate workstreams will find gaps between them at examination time.
Source: ABT client engagement data, 2024-2026
How Guardian Builds the Governance Foundation
Guardian is ABT's managed security and governance platform for M365 tenants. It does not deploy agents. Copilot Studio and Copilot Cowork handle that. What Guardian does is build the hardened tenant foundation that makes agent deployment safe for regulated environments.
Before Agent 365 goes live, Guardian addresses the prerequisites that most FIs have not completed:
Guardian's hardening templates cover 160+ Microsoft Secure Score controls across 11 categories. Agents inherit tenant security posture. A hardened tenant means agents start from a secure baseline, not from whatever default Microsoft shipped.
Purview sensitivity labels and DLP policies become agent data boundaries. Guardian configures these for financial services compliance requirements so agents cannot surface, process, or share data that carries restricted classifications.
Guardian monitors standing admin accounts through Security Insights and manages Conditional Access policies. When Agent 365 introduces Entra Agent IDs, these identity controls extend to cover agent identities alongside human ones.
Guardian Security Insights plus Microsoft's native Copilot analytics (prompt volume, active users, tool adoption) provide the observability layer that agent governance requires. Agent activity - surfaced via the M365 Copilot Data Connector for Sentinel (public preview) - feeds into the same Sentinel workspace and Guardian monitoring dashboards your compliance team already reviews.
Federal Reserve Supervisory Letter SR 11-7 applies to all AI and machine learning models used in banking, including the models that power AI agents in your tenant. Institutions that map Agent 365 controls to SR 11-7 requirements will be ahead of the examination curve. Institutions that wait until examiners ask will be playing catch-up.
Every partner can sell Copilot licenses. The governance foundation that makes AI safe to deploy in a regulated environment is what separates a vendor from a strategic partner.

The licensing path determines how your institution reaches agent governance, but the governance requirements are the same regardless of path. Whether your credit union deploys Copilot Business at $32 per user per month and adds Agent 365 later, or your 500-seat bank upgrades to E7 at $99 per user per month on May 1, Guardian is the governance layer for both. The $9 E5-to-E7 upgrade conversation is simple. The governance conversation is what makes it responsible.
Agent 365 is not an experiment to run in a sandbox and evaluate later. It is a production capability that changes how your institution interacts with data, makes decisions, and documents compliance. The institutions that build the governance foundation before May 1 will deploy agents with confidence. The ones that wait will deploy agents with risk.
Frequently Asked Questions
Agent 365 is Microsoft's governance framework for managing autonomous AI agents in M365 tenants. Copilot is the AI assistant that responds to prompts. Agent 365 provides the identity management, lifecycle controls, and audit infrastructure for agents built in Copilot Studio and executed through Copilot Cowork. Think of Copilot as the AI capability and Agent 365 as the governance layer that makes it safe to operate autonomously.
Agent 365 is available as a standalone add-on at $15 per user per month or bundled in the new M365 E7 Frontier Suite at $99 per user per month. E7 includes E5, Copilot, Agent 365, and the Entra Suite. For institutions already on E5, the upgrade is $9 per user per month during the promotional period. For SMB clients on Business Premium, the recommended path is to deploy Copilot Business first ($32/user/month with BP bundle) and add Agent 365 governance as agent adoption matures.
Multiple U.S. regulatory frameworks apply. Federal Reserve Supervisory Letter SR 11-7 covers all AI and machine learning models used in banking. OCC Bulletin 2023-17, the interagency guidance on third-party relationships published June 6, 2023, applies to the Anthropic sub-processor relationship in Copilot. The Treasury Department's Financial Services AI Risk Management Framework, published February 2026 with 230 control objectives, provides the most detailed AI governance guidance for financial institutions. State-level requirements like the Colorado AI Act (enforcement June 30, 2026) add additional obligations for institutions with customers in covered states.
Guardian does not deploy or manage agents directly. Copilot Studio and Copilot Cowork handle agent creation and execution. Guardian builds the hardened tenant foundation that makes agent deployment safe for regulated environments. This includes 160+ Secure Score controls, sensitivity labels and DLP policies that become agent data boundaries, identity governance through Conditional Access, and compliance monitoring through Guardian Security Insights alongside Microsoft's native Copilot analytics. Guardian is the governance layer; Agent 365 is the agent management layer.
Start with the five governance controls: configure Entra Agent ID policies, set data boundaries through sensitivity labels and DLP, establish lifecycle controls with approval workflows, configure audit trails for agent activity, and define human approval gates for high-risk actions. Update your vendor risk management program to document the Anthropic sub-processor relationship. Review your tenant security posture against Guardian's hardening baseline. Map Agent 365 controls to applicable regulatory requirements (SR 11-7, OCC 2023-17, Treasury AI RMF). Contact ABT for an AI Readiness assessment to identify gaps before agents go live.
Is Your Tenant Governed for Autonomous AI?
Agent 365 goes live May 1. ABT's governance assessment identifies the gaps between your current tenant configuration and what autonomous agents require in a regulated environment.

Justin Kirsch
CEO, Access Business Technologies
Justin Kirsch has led AI governance and Microsoft 365 security strategy for financial institutions since 1999. As CEO of Access Business Technologies, the largest Tier-1 Microsoft Cloud Solution Provider dedicated to financial services, he helps more than 750 credit unions, community banks, and mortgage companies build the governance foundations that make autonomous AI safe to deploy in regulated environments.