In This Article
- The 2026 Regulatory Landscape for Banks, Credit Unions, and Mortgage Lenders
- Five Pillars of a Compliant IT Framework
- Where M365 Guardian and Microsoft Purview Fit Inside the Framework
- The Cost of Getting It Wrong
- Building the Evidence Trail Examiners Actually Want
- NIST CSF 2.0 vs. CIS Controls vs. CISA CPGs
- The ABT Tier-1 CSP Advantage for Financial Institutions
- A 90-Day IT Framework Hardening Plan
- Frequently Asked Questions
A bank, credit union, or mortgage company with five business lines and a few dozen branches cannot examine itself by hand. The chief compliance officer cannot keep up. The IT team cannot keep up. Examiners notice. The institutions that pass clean exams have the same thing in common, one operational owner running the technical controls across every regulated entity in the institution, with a single console view, feeding the compliance team ready-to-use evidence. That operational owner is a Tier-1 Direct-Bill Cloud Solution Provider, and the operating model that sits on top of Microsoft 365 is what turns a generic tenant into a compliant IT framework. Access Business Technologies manages Microsoft 365 tenants for more than 750 financial institutions, and the framework described in this article is the same one we operate for them.
Why ABT Runs Compliant Frameworks for Financial Institutions
- FI-specific Microsoft Purview policies tuned to GLBA, FFIEC IT Examination Handbook, FTC Safeguards Rule, and Fannie Mae cybersecurity supplement requirements, not generic SMB defaults. Customer NPI, loan files, and supervisory correspondence each get their own retention and data-loss-prevention profile.
- Microsoft Entra ID Conditional Access baselines calibrated to community-bank and credit-union sign-in patterns, mortgage loan officer workflows, and branch-by-branch device posture rather than one-size-fits-all rules.
- Microsoft Sentinel deployment with analytic rules tuned to financial-services attack patterns, including business email compromise on closing wires, account takeover signals on online banking, and impersonation patterns targeting CFO and CCO accounts, rather than vendor-default rules.
The FFIEC sunset its Cybersecurity Assessment Tool on August 31, 2025, pushing financial institutions toward NIST CSF 2.0, CIS Controls v8.1, and the CISA Cybersecurity Performance Goals. Fannie Mae's Information Security and Business Resiliency Supplement has been fully enforceable for sellers and servicers since August 2025. The FTC Safeguards Rule, updated in 2023, is being enforced aggressively. The IT framework that worked five years ago will not pass the 2026 exam cycle, and the institutions that have not modernized their Microsoft 365 controls are the ones examiners are finding.
This article explains what a compliant IT framework looks like in 2026, where Microsoft 365 fits inside it, where ABT layers M365 Guardian and Microsoft Purview on top of the Microsoft baseline, and what a Tier-1 Direct-Bill Cloud Solution Provider does for an institution that needs the framework to actually pass an exam rather than just look complete on paper.
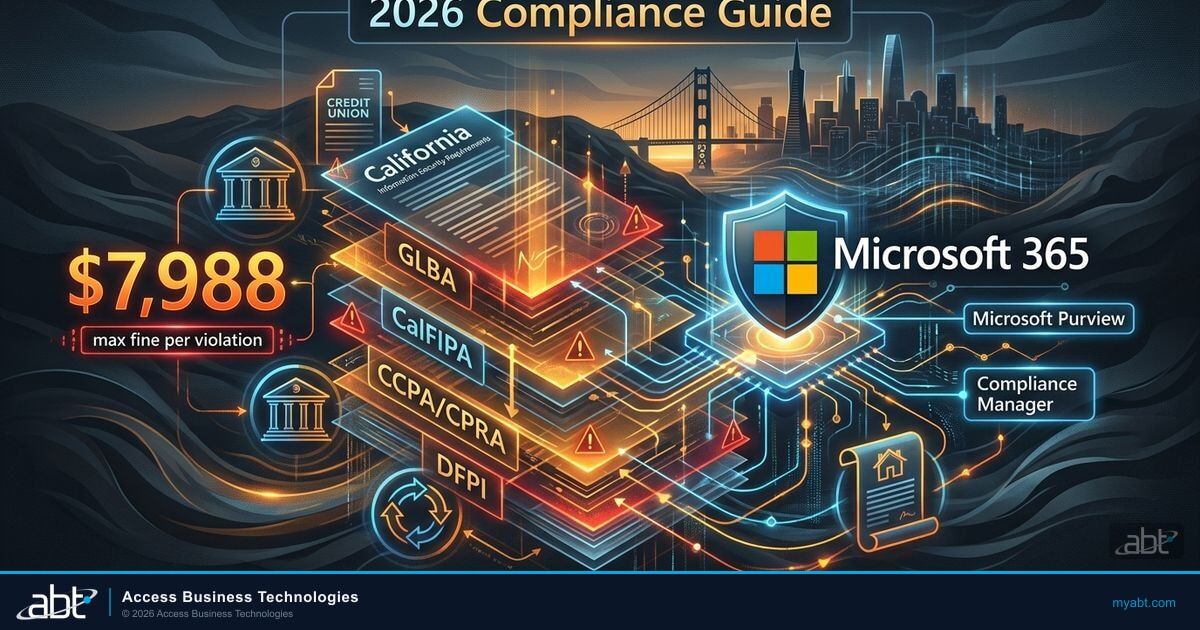
The 2026 Regulatory Landscape for Banks, Credit Unions, and Mortgage Lenders
Financial institutions operate under overlapping federal and state regulations. The Gramm-Leach-Bliley Act (GLBA), Dodd-Frank Act, RESPA, TILA, and HMDA set the federal floor for lenders. Banks add FDIC, OCC, and state-charter oversight. Credit unions answer to NCUA. Mortgage companies layer in Fannie Mae and Freddie Mac requirements through their seller-servicer agreements. The FTC Safeguards Rule applies across the entire non-bank financial sector. State regulators add their own privacy and security expectations on top.
The biggest single shift in 2025 and 2026 is the post-CAT compliance framework. The FFIEC retired the Cybersecurity Assessment Tool and now points institutions toward three alternatives.
- NIST Cybersecurity Framework 2.0 with its six core functions: Govern, Identify, Protect, Detect, Respond, Recover. The Govern function is new in 2.0 and is what most institutions are still working to operationalize.
- CISA Cybersecurity Performance Goals 2.0 including the financial-services sector-specific targets that overlay the cross-sector goals.
- CIS Controls v8.1 providing prioritized technical safeguards ranked by implementation group, with IG1 covering essential cyber hygiene and IG2 adding controls for organizations managing sensitive data such as customer NPI and loan files.
Fannie Mae's Information Security and Business Resiliency Supplement compounds the pressure. Sellers and servicers must now maintain documented business continuity plans that specifically address cyber incidents, multi-factor authentication enforced firm-wide, least-privilege access controls, and a 36-hour incident reporting deadline to Fannie Mae after identifying any cybersecurity event. Technology service providers had until December 31, 2025 to comply. Document custodians have until April 1, 2026.
Why This Matters Right Now
The Identity Theft Resource Center recorded 739 data compromises in the financial services sector in 2025, more than any other industry for the second year running. Several financial institutions disclosed breaches in early 2026 alone, with one mortgage lender reporting that a 2023 compromise was not discovered until late 2025, more than two years of undetected exposure. None of these institutions believed their controls were inadequate at the time. The pattern is what examiners are now organizing their cycle exams around.
For an institution's IT team, the practical consequence is that a framework built around the CAT five years ago is now outdated. Examiners expect to see alignment with one of the FFIEC-endorsed frameworks, a documented current-year risk assessment, evidence of continuous monitoring, and the records to prove that the technical controls described in the institution's information security policy are actually in production and tested. That last clause is where most institutions fail.
Five Pillars of a Compliant IT Framework
A compliant IT framework rests on five pillars. Skip one and the whole structure wobbles during an exam.
1. Identity and Access Management
Every compliance framework starts with controlling who can access what. For institutions handling customer NPI, Social Security numbers, account numbers, and loan files, weak access controls are the fastest path to a finding.
The technical requirements include multi-factor authentication on every system that touches customer data including the loan origination system, document management, and email; Conditional Access policies in Microsoft Entra ID that block legacy authentication protocols and enforce device compliance before allowing sign-in; role-based access control so loan officers see loan data and not payroll records; and privileged access management for admin accounts with time-limited elevation and full audit logging.
Microsoft Entra ID handles all four when configured correctly. The gap most institutions face is not missing tools, it is incomplete configuration. The tenant has the capabilities. The question is whether someone has turned them on, tested them, and documented the tests in a form an examiner will accept.
2. Data Protection and Encryption
The FTC Safeguards Rule explicitly requires encryption of customer information both in transit and at rest. That means TLS 1.2 or higher for transmission and AES-256 for storage. Microsoft 365 supplies the cryptographic primitives. The compliance work is configuring the data plane so the right data gets the right protection.
Practical steps include enabling BitLocker on every endpoint through Microsoft Intune device compliance policies; configuring Microsoft Purview Data Loss Prevention policies to prevent customer NPI, Social Security numbers, and account numbers from leaving the institution via email or external file sharing; applying Microsoft Purview sensitivity labels to loan files and other regulated documents so encryption follows the file when it moves; and verifying that the loan origination system vendor's encryption standards match the institution's policy when data transits between the institution's network and the vendor's cloud.
3. Continuous Monitoring and Threat Detection
Annual penetration tests are no longer sufficient. The NIST CSF 2.0 Detect function expects continuous monitoring with automated alerting. For financial institutions, that means real-time visibility into sign-in anomalies and impossible travel detections; changes to Conditional Access policies or admin role assignments; external sharing of sensitive documents in SharePoint Online and OneDrive; endpoint compliance drift, where devices fall out of compliance with Intune policies; and email authentication failures across SPF, DKIM, and DMARC.
Microsoft Defender for Office 365 and Microsoft Defender for Endpoint provide the detection layer. Microsoft Sentinel aggregates the signals across the environment into a single incident timeline. The challenge for institutions with two-person or three-person IT teams is having someone watching the dashboard. Alerts that fire into an unmonitored inbox are worse than no alerts at all because examiners will ask to see the response logs.
4. Incident Response and Business Continuity
Examiners want to see three artifacts in the incident response surface: a written incident response plan that names roles, escalation procedures, and communication templates; tabletop exercises conducted at least annually with documented results and tracked corrective actions; and backup and recovery testing that proves the institution can restore loan data and resume operations within its stated recovery time objective.
The common failure point is testing. Many institutions have an incident response plan in a binder on a shelf. They have never run it. When examiners ask when the plan was last tested, the answer cannot be never.
5. Vendor Risk Management
Financial institutions rely on dozens of third-party vendors, from loan origination platforms and credit bureaus to appraisal management companies, document preparation services, and IT providers. Each vendor with access to customer data extends the institution's compliance boundary.
A compliant vendor management program includes due diligence questionnaires for every vendor with data access, annual SOC 2 Type II report reviews or equivalent attestations, contractual breach notification timelines that match the institution's regulatory obligations, and access reviews confirming that vendors only reach the systems they actually need. The FFIEC's updated guidance specifically calls out concentration risk, so if the loan origination system, email, file storage, and security tools all run on the same cloud provider, examiners want to see how the institution has assessed and mitigated that concentration.
Where M365 Guardian and Microsoft Purview Fit Inside the Framework
Microsoft 365 supplies the building blocks for every pillar. Microsoft Entra ID covers identity. Microsoft Intune covers device posture. Microsoft Defender covers threat detection. Microsoft Sentinel covers SIEM. Microsoft Purview covers data classification, data loss prevention, audit logging, and retention. These are the same components every financial institution running on Microsoft 365 has access to. The difference between a framework that passes an exam and one that draws findings is not which components are licensed. It is how they are configured, monitored, and documented across the institution's full footprint.
That is where the operating model matters. ABT calls our operating model on top of the Microsoft baseline M365 Guardian. Guardian is not a separate product the institution licenses. It is the configuration, monitoring, and evidence-generation layer that a Tier-1 Direct-Bill Cloud Solution Provider applies to the institution's Microsoft 365 tenant, calibrated for the regulatory regime the institution actually operates under. For a community bank, Guardian configures the Microsoft Defender suite around FFIEC IT Examination Handbook expectations and the bank's own concentration-risk profile. For a credit union, Guardian calibrates the Microsoft Entra ID Conditional Access baseline to NCUA cybersecurity assessment expectations and member online banking patterns. For a mortgage company, Guardian tunes Microsoft Purview retention to Fannie Mae and Freddie Mac selling and servicing requirements and the FTC Safeguards Rule.
Microsoft Purview is the layer that does most of the work in the audit-evidence surface. Purview Audit produces the time-stamped trail of every create, modify, and delete action across Exchange Online, SharePoint Online, OneDrive, Microsoft Teams, and Microsoft Entra ID. Purview Audit Premium extends retention from the default to one year with the option to extend further. Purview Data Loss Prevention policies block exfiltration of customer NPI, account numbers, Social Security numbers, and loan application data across email, Teams chat, OneDrive sharing, and endpoint exfiltration channels. Purview Information Protection sensitivity labels travel with the file, so a loan file marked Confidential carries its encryption and access controls into wherever the file moves. Purview Communication Compliance lets the institution sample, classify, and review business communications for off-channel behavior. Purview Retention policies hold customer correspondence, loan files, and supervisory records for the durations the institution's regulators require. Compliance Manager templates map the institution's actual control state to NIST CSF 2.0, CIS Controls, GLBA, FTC Safeguards Rule, and the Fannie Mae supplement.
Microsoft Purview is the spine of a defensible IT framework for a financial institution. It produces the audit evidence (Purview Audit Premium), enforces the data classification (Information Protection sensitivity labels), prevents the exfiltration (Data Loss Prevention), and holds the records (Retention policies and Litigation Hold). Microsoft Entra ID supplies the identity layer with Conditional Access enforcing MFA, blocking legacy authentication, and gating sign-in by device posture. Microsoft Intune enrolls and posture-checks every device that touches customer data. Microsoft Defender for Office 365 and Microsoft Defender for Endpoint handle the active threat side. Microsoft Sentinel aggregates the signals into a single SIEM that satisfies the incident detection and response evidence requirements regulators expect. ABT applies M365 Guardian, our financial-services-tuned operating model for these Microsoft tools, on top of every customer tenant so the institution gets a calibrated framework on day one rather than a generic tenant the IT team has to configure from scratch.
The Cost of Getting It Wrong
Compliance failures in financial services carry compounding consequences. The direct costs are measurable. The indirect costs, operational disruption, reputational damage, and lost business, are harder to quantify but often larger.
That $6.08 million figure does not count the operational damage that follows an examination finding. Examination findings require documented remediation plans with deadlines. The IT team stops building and starts fixing. Loan officers, branch staff, and member services wait for system changes. FTC enforcement under the Safeguards Rule can impose penalties up to $43,000 per day for consent order violations. The FTC also requires breach notification within 30 days for incidents affecting 500 or more consumers. Warehouse lenders are tightening their cybersecurity attestation requirements before extending credit lines, so a failed exam can restrict an institution's funding sources. Fannie Mae's 36-hour incident reporting deadline means that a breach which used to be quietly managed now becomes an immediate disclosure obligation.
The average breach lifecycle in financial services is 241 days from intrusion to containment, a nine-year low but still eight months of undetected exposure. For institutions without mature detection capabilities, the actual lifecycle is likely longer.
The CSF has been a vital tool for many organizations, helping them anticipate and deal with cybersecurity threats. CSF 2.0 is not just about one document. It is about a suite of resources that can be customized and used individually or in combination over time as an organization's cybersecurity needs change and its capabilities evolve.
Building the Evidence Trail Examiners Actually Want
Compliance is not just about having controls. It is about proving they work. The IT framework has to generate evidence automatically because manual compliance tracking breaks down at scale.
Microsoft 365 compliance tools can produce most of the evidence examiners request, and a Tier-1 Direct-Bill Cloud Solution Provider configures them to do so by default rather than only when the institution is preparing for an exam. The key reports include Microsoft Secure Score trending over time, which shows continuous improvement rather than a point-in-time snapshot; Microsoft Entra ID Conditional Access sign-in logs showing MFA enforcement rates and blocked legacy authentication attempts; Microsoft Purview DLP policy match reports demonstrating that the institution is catching and blocking sensitive data leaks; Microsoft Intune device compliance reports showing encryption status, OS patch levels, and policy adherence; and Microsoft Purview Audit Premium logs covering admin actions, mailbox access, and SharePoint and OneDrive external sharing across the institution's tenant.
A cycle exam opens at a multi-branch credit union. The examiner asks for retention configurations and audit logs across all branches for a 24-month lookback. The CCO emails the IT contact. The IT contact pulls reports manually from the Microsoft 365 admin center, takes two weeks to assemble a spreadsheet, and discovers that Purview Audit Premium was only enabled on the headquarters tenant, not the branch tenant. The exam extends into a second sweep. The institution receives a finding for inconsistent retention.
The same exam opens. ABT pulls a cross-tenant configuration report from the operating-model dashboard that shows the applied baseline, the active Purview retention policies, the Conditional Access state, and the Microsoft Defender posture across every tenant the institution operates. The CCO produces the Purview Audit Premium log extracts on demand. The exam closes on time. The institution has no finding on this surface.
The trick is having those reports already running before an exam, not scrambling to pull them when the notification letter arrives. ABT builds the monthly compliance dashboard and the institution's CISO or compliance officer reviews it. That review itself becomes evidence of governance, which is exactly what the NIST CSF 2.0 Govern function expects to see.
Policies are the other half of the evidence trail. Examiners read policies. They compare what the policy says to what the system actually does. The fastest way to fail an exam is having a policy that describes controls that have not been implemented. If the policy says all endpoints are encrypted but Intune shows 15% non-compliant devices, that is a finding. The policy and the system have to match, which is why a managed deployment that keeps both in sync is the cleanest route.
Get a Financial Institution Compliance Framework Assessment
ABT operates the M365 Guardian framework described in this article for banks, credit unions, and mortgage companies across the United States. A 30-minute conversation maps your current Microsoft 365 tenant configuration, surfaces the Microsoft Purview and Entra ID gaps your next examiner is most likely to find, and outlines what a Tier-1 Direct-Bill CSP-managed framework would cover. No commitment, no quote, no obligation.
NIST CSF 2.0 vs. CIS Controls vs. CISA CPGs: Which Framework Fits Your Institution
With the FFIEC CAT retired, every financial institution has to choose a replacement framework. Each option serves a different organizational profile.
| Dimension | NIST CSF 2.0 | CIS Controls v8.1 | CISA CPGs 2.0 |
|---|---|---|---|
| Best for | Mid-to-large institutions with compliance staff | Smaller institutions wanting prioritized quick wins | Institutions needing a minimal baseline as a starting point |
| Structure | 6 functions, 22 categories, 106 subcategories | 18 controls, 153 safeguards in 3 implementation groups | 37 cross-sector goals plus financial-services additions |
| Examiner recognition | Highest, FFIEC primary recommendation | Accepted by most examiners as the prioritization layer | Growing but newer; usually paired, not used alone |
| Implementation effort | High, requires mapping to the institution's environment | Medium, prescriptive and actionable per safeguard | Low, designed as a floor rather than a ceiling |
| Regulatory mapping | Strong; maps to FFIEC, GLBA, FTC Safeguards Rule | Good; maps to NIST CSF, PCI DSS, and sector overlays | Limited; cross-sector minimum, paired with NIST or CIS |
Most financial institutions end up with NIST CSF 2.0 as the primary framework and CIS Controls v8.1 as the prioritization layer. The CIS Controls' three implementation groups provide a natural roadmap. IG1 covers essential cyber hygiene that every institution needs. IG2 adds controls for organizations managing sensitive data, which is where most community banks, credit unions, and mortgage companies should target. IG3 covers advanced threats and is appropriate for larger institutions with mature security programs. Whichever framework an institution adopts, the decision has to be documented, the rationale captured, and the mapping to the institution's specific regulatory obligations recorded. Examiners do not require a specific framework. They require a defensible choice backed by evidence.
For institutions that need a deeper look at how Microsoft 365 generates the audit evidence on top of any of these frameworks, see our writeup on business intelligence for financial institutions, which covers the dashboards and reporting patterns that turn compliance metrics into operational signals.
The ABT Tier-1 CSP Advantage for Financial Institutions
Tier-1 Direct-Bill Cloud Solution Provider is Microsoft's top program tier for partners. Only a small fraction of the Microsoft CSP ecosystem qualifies. A Direct-Bill partner transacts directly with Microsoft, holds dedicated support engineers, and is operationally accountable to Microsoft for how customer tenants are configured and run. It is the difference between a partner who resells Microsoft licenses and a partner Microsoft trusts to operate enterprise-grade tenants at scale. For a community bank, a credit union, or a mortgage company choosing a CSP, Tier-1 Direct-Bill is a fast first-pass filter.
Access Business Technologies is a Tier-1 Microsoft Cloud Solution Provider that manages Microsoft 365 tenants for more than 750 financial institutions. Our footprint covers banks, credit unions, mortgage companies, and securities firms operating under federal and state regulatory oversight. The compliant IT framework described in this article is the same one we operate for our customers, layered with M365 Guardian as our financial-services-tuned operating model on top of the Microsoft baseline.
What the institution experiences are the outcomes. Consistent Microsoft Entra ID Conditional Access policies enforcing MFA across every user account. Microsoft Intune device compliance applied to every laptop, workstation, and mobile device that touches customer data. Microsoft Defender for Office 365 and Defender for Endpoint tuned to financial-services attack patterns. Microsoft Purview Audit Premium, DLP, sensitivity labels, retention policies, and Communication Compliance configured to the regulations the institution actually operates under. Microsoft Sentinel aggregating the signals into incident timelines that produce evidence on demand. And the monthly compliance dashboard the institution's CISO or CCO walks the examiner through, instead of a binder of policies that have not been touched since the last cycle.
The institution continues to own its regulatory relationships, customer accounts, and registered employees. The partner relationship with ABT runs under Granular Delegated Administrative Privileges with least-privilege role grants, an executed vendor oversight agreement that satisfies the FTC Safeguards Rule and amended Regulation S-P third-party expectations, and an annual independent verification cycle that produces the evidence the institution's CCO needs for the institution's own examination prep. For more on how that operating model handles the loan-platform side of the institution's footprint, see our writeup on the mortgage pipeline integration pattern across loan origination systems, core banking, and the Microsoft 365 audit layer.
A 90-Day IT Framework Hardening Plan
For an institution whose framework has gaps, the closing-the-gap work splits naturally into three 30-day blocks. The order matters because identity has to settle before device posture is meaningful, device posture has to settle before threat detection becomes signal rather than noise, and the documentation has to follow the controls rather than describe what the IT team intends to do later.
Enable MFA for every user account including service accounts where the workflow allows it. Block legacy authentication via Conditional Access in Grant mode, not Report-Only mode. Audit admin role assignments in Microsoft Entra ID and remove unnecessary privileged access. Implement named Conditional Access policies for each user group rather than relying on default policies that examiners can read but cannot find in the institution's documentation.
Enable BitLocker enforcement on every endpoint through Microsoft Intune device compliance policies. Deploy Microsoft Purview DLP policies targeting Social Security numbers, account numbers, and loan application data across email, Teams chat, OneDrive, and endpoint channels. Apply Microsoft Purview sensitivity labels to the loan file workflow and other regulated document types. Configure Microsoft Defender for Office 365 and Defender for Endpoint alerting and assign named response owners on the institution's IT or compliance team.
Stand up Microsoft Sentinel as the SIEM of record, with analytic rules tuned to financial-services attack patterns including business email compromise on closing wires and account takeover signals on online banking. Configure Microsoft Purview Audit Premium for one-year retention. Write or update the institution's Information Security Policy so it matches the controls now in production. Run a tabletop incident response exercise. Test backup restoration and document the recovery time objective and recovery point objective results. Complete vendor risk assessments for the top ten data-access vendors.
Key Takeaway
A compliant IT framework is not a binder on a shelf. It is the Microsoft Entra ID, Microsoft Intune, Microsoft Defender, Microsoft Purview, and Microsoft Sentinel surface, configured consistently, monitored continuously, and documented in a form that examiners accept. The Tier-1 Direct-Bill Cloud Solution Provider that runs that surface for the institution is the operational owner that turns the framework from a policy document into a working system. M365 Guardian is ABT's operating model for doing exactly that across 750+ financial institutions.

Frequently Asked Questions
The FFIEC retired the Cybersecurity Assessment Tool on August 31, 2025 and now endorses three alternatives: NIST Cybersecurity Framework 2.0, the CISA Cybersecurity Performance Goals, and CIS Controls v8.1. Banks, credit unions, and mortgage companies should align with at least one of these frameworks, document the choice and the rationale, and produce risk assessments mapped to the chosen framework's control categories. Examiners expect to see framework alignment in the next examination cycle, and the institutions that have not made the transition are the ones drawing findings.
Microsoft Purview is the layer inside Microsoft 365 that handles the audit-evidence side of a compliance framework. Purview Audit produces the time-stamped audit log across Exchange Online, SharePoint Online, OneDrive, Microsoft Teams, and Microsoft Entra ID. Purview Audit Premium extends retention to one year with the option to extend further. Purview Data Loss Prevention prevents exfiltration of customer NPI, Social Security numbers, account numbers, and loan files. Purview Information Protection sensitivity labels attach encryption and access controls that travel with the file. Purview Retention policies bind tamper-evident retention to mailboxes, sites, channels, and devices. Purview Communication Compliance lets the institution sample and review business communications for off-channel behavior. Together, Purview is the spine of the evidence trail examiners ask for during a cycle exam.
M365 Guardian is ABT's operating model on top of Microsoft 365 for financial institutions. It is not a separate product the institution licenses from Microsoft. It is the configuration, monitoring, and evidence-generation layer that a Tier-1 Direct-Bill Cloud Solution Provider applies to the customer's tenant. Guardian takes the Microsoft components the institution already pays for, including Microsoft Entra ID, Microsoft Intune, Microsoft Defender for Office 365 and Defender for Endpoint, Microsoft Sentinel, and Microsoft Purview, and configures them as a calibrated set of controls aligned to the institution's regulatory regime, monitored by ABT's security team, and producing evidence the institution's CCO can hand to an examiner without a two-week scramble.
The FTC Safeguards Rule requires non-bank financial institutions, including mortgage companies and finance companies, to implement specific technical controls. The required controls include encryption of customer data both in transit and at rest, multi-factor authentication on every system that accesses customer information, continuous monitoring or annual penetration testing plus biannual vulnerability assessments, a written incident response plan, and oversight of third-party service providers that have access to customer data. Non-compliance can result in FTC enforcement actions, penalties up to $43,000 per day for consent order violations, and breach notification obligations within 30 days for incidents affecting 500 or more consumers.
An institution's incident response plan must include named roles and responsibilities, escalation procedures with current contact information, communication templates for regulators and affected customers, evidence preservation procedures aligned to legal hold expectations, and recovery steps with documented recovery time and recovery point objectives. The plan must be tested at least annually through a tabletop exercise with documented results and corrective actions tracked to completion. For mortgage companies operating under the Fannie Mae Information Security and Business Resiliency Supplement, the plan must also build in the 36-hour incident reporting deadline to Fannie Mae after identifying any cybersecurity event.
Financial institutions should update IT risk assessments at least annually and whenever significant changes occur. Significant changes include deploying a new loan origination system, migrating to cloud infrastructure, opening or closing branch offices, acquiring or merging with another institution, experiencing a security incident, or adopting a new framework such as NIST CSF 2.0. A risk assessment older than 12 months will draw examiner scrutiny during any regulatory review, and a risk assessment that does not reflect the institution's current environment will draw findings even if it was updated within the past year.

Justin Kirsch
CEO, Access Business Technologies
Justin Kirsch has guided Microsoft deployments for regulated financial institutions since 1999. As CEO of Access Business Technologies, the largest Tier-1 Microsoft Cloud Solution Provider dedicated to financial services, he helps more than 750 banks, credit unions, mortgage companies, and securities firms standardize their Microsoft 365 tenants for examination readiness without slowing down how the business actually works.