In This Article
- Same Security Posture as a Billion-Dollar Bank, Sized for a Five-Person Clinic
- Why Healthcare Carries Concentrated Risk on a Small IT Budget
- What "Tier 1 CSP" Actually Means: Manage Not Host
- The October 2025 Microsoft Policy Change Most Practices Missed
- The Math: Enterprise Security Under $200 a Month for a Typical Small Clinic
- The July 2026 Deadline Worth Calendaring
- Guardian for Healthcare: The Operating Model Behind the License
- Frequently Asked Questions
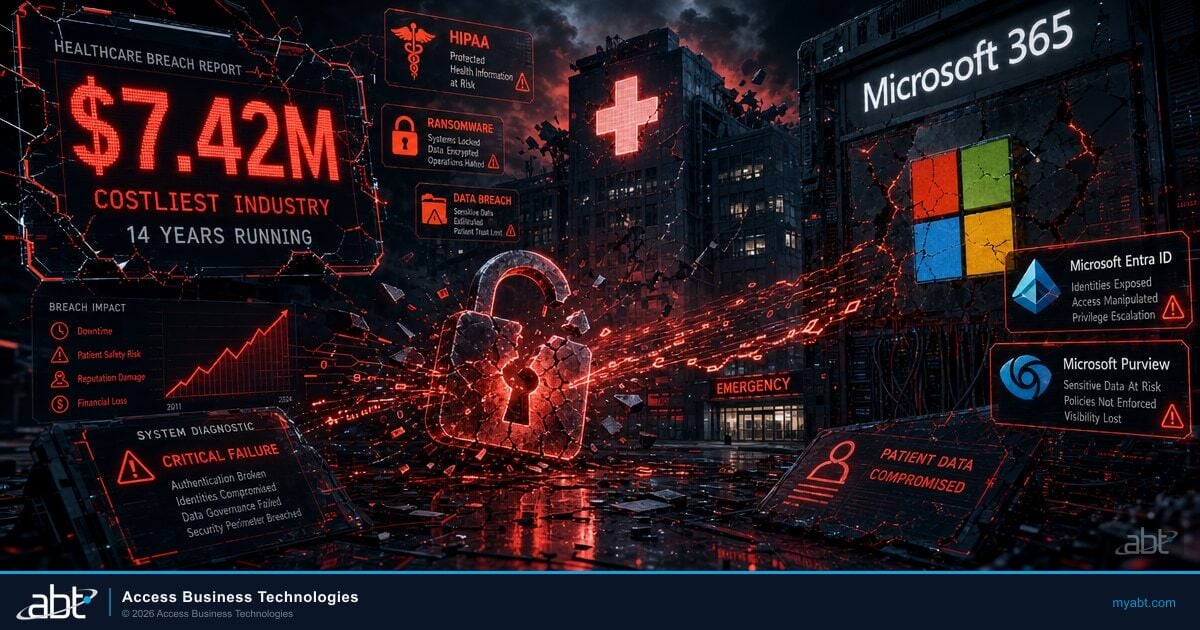
Most healthcare practices operate with an IT budget that is a tenth of what a community bank spends on the same problem. The patient records in your Microsoft 365 tenant are worth roughly the same to attackers as a deposit ledger. HIPAA examiners and the Office for Civil Rights expect the same configuration discipline. That asymmetry is the structural reason 14 years of IBM breach-cost reports keep landing healthcare at the top of the list.
The fix is not more spend. The fix is correct configuration on the Microsoft licenses most practices already own, layered with the operating discipline examiners actually inspect against. The license itself is a flat list price. The configuration, monitoring, and audit-ready evidence trail are the part that separates a practice from a settlement.
This article walks through the architecture story behind that work, why a Tier 1 Microsoft Cloud Solution Provider is structurally positioned to do it, what it means that ABT manages your Microsoft 365 tenant rather than hosting it, the October 2025 Microsoft non-profit eligibility change most practices have not heard about, and the math that puts a credible HIPAA-grade security stack inside the budget of a five-person clinic.
Same Security Posture as a Billion-Dollar Bank, Sized for a Five-Person Clinic
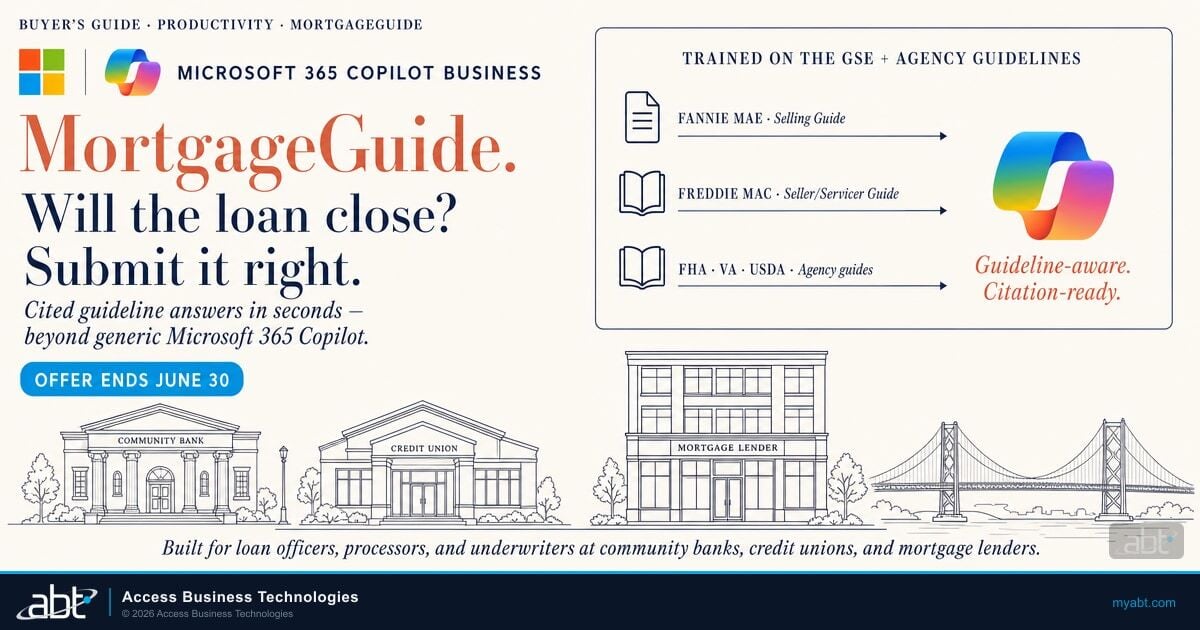
ABT manages Microsoft 365 tenants for more than 750 highly regulated organizations. The bulk of that book is community banks, credit unions, and mortgage companies operating under FFIEC examination discipline. The operating model that grew up there, hardening every tenant against the configuration examiners actually inspect against, then monitoring it daily for drift, then producing the audit-ready evidence trail when a regulator walks in, is the same operating model healthcare practices need under the HIPAA Security Rule and the Office for Civil Rights settlement pattern.
The technical posture is identical because the underlying Microsoft platform is identical. Microsoft's HIPAA Business Associate Agreement applies automatically to any customer who qualifies as a covered entity or business associate, covering Exchange Online, OneDrive, Teams, SharePoint, Microsoft 365 Copilot, Defender for Office 365, Microsoft Entra ID, Microsoft Purview, and most Azure services. The same Conditional Access policies that block legacy authentication for a credit union teller block it for a clinic medical assistant. The same Microsoft Purview audit log retention that satisfies an OCC examiner satisfies an OCR investigator. Microsoft does not run a separate, lesser version of the security platform for small organizations.
Why Healthcare Practices Win on This Architecture
A 50-person clinic and a $5B community bank both license Microsoft Entra ID Conditional Access, Microsoft Defender for Office 365, Microsoft Purview audit logging, and Microsoft Intune device management from the same Microsoft tenant catalog. The configuration discipline that protects deposit data protects protected health information. The cost difference between getting it right and getting it wrong is the difference between $5 a user a month and a $1 million settlement.
The asymmetry runs the other direction on cost. A bank IT department with 20 administrators and a 7-figure security budget can build the configuration and monitoring discipline in-house. A five-person physician practice cannot. That is the wedge a Tier 1 CSP fills. The CSP runs the operating model. The practice buys an outcome.
Why Healthcare Carries Concentrated Risk on a Small IT Budget
Three structural conditions concentrate risk in healthcare in a way that no other industry shares at the same intensity:
- Protected health information is the highest-value record on the dark web. A complete patient record includes financial identifiers, insurance numbers, and medical history that does not expire. IBM puts the per-record cost of a healthcare breach at $398, the highest of any industry tracked.
- Clinical operations cannot tolerate downtime. A bank can revert to paper for a day. A hospital cannot divert ambulances for a week without losing a season of revenue. Ransomware payments become rational in the moment.
- Vendor sprawl is structural. The average healthcare organization runs hundreds of connected vendors, devices, and applications. Examiners hold the provider accountable for every one of them. The Change Healthcare incident entered through a remote-access portal that did not require multi-factor authentication.
Layered on top of those three conditions is a regulatory enforcement environment that has been sharpening across 2025 and into 2026. The Office for Civil Rights has been very explicit about what it expects to find when it walks into a covered entity after a breach. Five recent settlements (BayCare Health System, Assured Imaging, Axia Women's Health, Star Group, SG Health Plan) all cite the same phrase: a failure to conduct an accurate and thorough risk analysis of vulnerabilities to electronic protected health information. OCR is not citing these entities for the ransomware. OCR is citing them for not knowing the ransomware could happen.
For practices running Microsoft 365 under a signed BAA, that gap is a configuration and monitoring problem, not a procurement problem. The Microsoft platform ships with every control a HIPAA-aligned tenant needs. The work is turning the controls on, tuning them against a documented baseline, monitoring them for drift, and producing the evidence trail OCR asks for the day after a breach.
Healthcare practices are not under-licensed. They are under-configured. The fix is the operating model around the license, not another vendor relationship.
What "Tier 1 CSP" Actually Means: Manage Not Host
The phrase "Tier 1 Microsoft Cloud Solution Provider" carries a specific contractual meaning that matters for healthcare data architecture. Tier 1 CSPs hold a direct partnership with Microsoft (no second-tier distributor between the CSP and the Microsoft commerce platform). The CSP transacts every license, every subscription, every Azure subscription with Microsoft directly. The CSP also accepts the support obligations and the security posture commitments Microsoft requires of direct partners.
The second piece of vocabulary matters even more for HIPAA. ABT manages your Microsoft 365 tenant via delegated administration. The distinction between managing a tenant and hosting infrastructure is canonical Microsoft framing, with direct architectural consequences for how patient data is protected.
Microsoft 365 Tenant (Manage)
- Your Microsoft 365 tenant is your environment, with your data inside it
- Microsoft 365 is the platform; ABT applies the configuration discipline that makes it HIPAA-ready
- ABT manages your tenant via delegated administration (GDAP): configuration access, not data access
- Your data isolation is structural: the tenant is yours, the audit trail is yours, the controls are yours
Azure Environment (Host)
- Your Azure subscription is customer-controlled cloud infrastructure
- ABT operates the Azure workloads (FHIR servers, backup, DR, custom apps) as your partner of record
- ABT is the host for Azure-resident workloads under the same Microsoft BAA
- The combined statement: "We manage your Microsoft 365 tenant. We host your Azure environment."
The practical consequence for a healthcare practice is straightforward. Your patient data lives inside your Microsoft 365 tenant under Microsoft's BAA, with ABT performing the configuration and monitoring work via delegated admin. That is a different security architecture than the legacy "managed IT" pattern of pulling customer data into the MSP's environment for backup, mailbox archiving, or remote access proxying. Those legacy patterns are still common in healthcare IT. They are also what auditors and breach investigators flag as elevated risk.
A Tier 1 CSP under delegated admin holds configuration permissions on your tenant, not a copy of your data. Patient records, claims, clinical notes, scheduling data, and email stay inside your Microsoft 365 tenant under Microsoft's HIPAA BAA commitments.
Your data lives inside Microsoft Entra ID Conditional Access policies you set, behind Microsoft Purview Information Protection labels and DLP policies tuned to your patient population, with an audit log trail OCR expects to see. The Tier 1 CSP relationship gives you that posture through a delegated-admin model that scopes the partner's access to configuration tasks. We make the tenant secure; the tenant stays yours.
This is the architectural difference that makes the Tier 1 CSP relationship structurally safer for HIPAA workloads than a traditional MSP relationship. The traditional MSP often owns mailbox copies, backup repositories, monitoring agent telemetry, and customer credentials inside its own infrastructure. A breach of the MSP becomes a breach of every customer. Under the Microsoft delegated admin model, the CSP holds configuration rights, not data. The two architectures look similar in a vendor pitch and look very different in a HIPAA risk analysis.
Per Microsoft Learn: Cloud Solution Providers manage customer Microsoft 365 tenants rather than host them. For healthcare, that distinction is the architectural separation between patient data (inside your tenant under Microsoft's HIPAA BAA) and tenant configuration (managed by the partner via delegated administration).
The October 2025 Microsoft Policy Change Most Practices Missed
In October 2025, Microsoft agreed to a substantial change in how its non-profit eligibility program operates. Two specific items were removed from the eligibility framework, and the practical effect for healthcare 501(c)(3) organizations is broader access to the same enterprise-grade Microsoft platform at non-profit pricing.
The first change removed the categorical exclusion that had blocked certain healthcare orgs from the non-profit program. The second change removed the ideological attestation requirement that the program had used as a screening filter. The result is a more content-neutral eligibility process. If an organization is a U.S. 501(c)(3) with a community-benefit health mission, it qualifies. The Microsoft platform does not apply values-based screening as a condition of program participation.
What This Means for a Healthcare 501(c)(3)
If your organization holds 501(c)(3) status and provides community-benefit health services, you almost certainly qualify for Microsoft non-profit pricing on Microsoft 365, Azure, and the security stack. Free clinics, federally qualified health centers, rural health clinics, behavioral health nonprofits, dental nonprofit clinics, specialty clinics, and skilled nursing facilities are all explicitly listed. Verification is administrative (Microsoft uses Goodstack to confirm your IRS status), not editorial.
For practices already running Microsoft 365 commercial pricing, the transition is straightforward. Your organization registers at nonprofit.microsoft.com, completes Goodstack validation in approximately three business days, generates a Microsoft certificate of eligibility, and forwards it to your CSP. Your CSP provisions the non-profit SKUs through Microsoft Partner Center. The non-profit licenses replace the commercial licenses at the next renewal. No tenant migration, no data move, no service interruption.
The implementation has been uneven during the transition window. Some applications approve cleanly. Some still hit stale screening systems. A Tier 1 CSP with regular Microsoft channel contact can escalate denials that look inconsistent with the October 2025 policy. That escalation path is part of what the CSP relationship buys.
The Math: Enterprise Security Under $200 a Month for a Typical Small Clinic
The non-profit pricing changes the budget arithmetic for small healthcare orgs in a meaningful way. Microsoft 365 Business Basic for Nonprofits is free up to 300 seats. Microsoft 365 Business Premium for Nonprofits is $5.50 per user per month, roughly 75% off the commercial $22 list price. Azure for Nonprofits provides a $2,000 annual credit, renewable annually. The Microsoft HIPAA BAA is included by default, no separate signing required.
| SKU | Commercial | Nonprofit | Discount |
|---|---|---|---|
| Microsoft 365 Business Basic | $6.00 / user / mo | Free (up to 300 seats) | 100% |
| Microsoft 365 Business Premium | $22.00 / user / mo | $5.50 / user / mo | 75% |
| Microsoft 365 E3 | $36.00 / user / mo | $9.00 / user / mo | 75% |
| Microsoft 365 E5 | $57.00 / user / mo | $22.80 / user / mo | 60% |
| Microsoft Defender for Office 365 Plan 2 | $5.00 / user / mo | $2.00 / user / mo | 60% |
| Microsoft Intune Plan 1 | $8.00 / user / mo | $1.50 / user / mo | 81% |
| Azure annual credit | N/A | $2,000 / year | Grant |
For a 25-employee community health center on a HIPAA-covered footing, a credible non-profit license stack looks like this: Microsoft 365 Business Premium for Nonprofits at $5.50 a seat for the productivity core (Outlook, Word, Excel, Teams, SharePoint, OneDrive, plus Microsoft Defender for Business, Microsoft Intune Plan 1, Microsoft Entra ID P1, and Microsoft Purview Information Protection P1 bundled in), Microsoft Defender for Office 365 Plan 2 at $2.00 a seat for upgraded email security, and the Azure $2,000 annual credit for ancillary infrastructure. Total license cost: approximately $187 a month for 25 users on a HIPAA-aligned Microsoft stack with multi-factor authentication, Conditional Access, audit logging, DLP, and device management in place.
The Math That Changes the Conversation
$187 a month buys a 25-person community clinic the same Microsoft platform foundation a $5B community bank uses to satisfy FFIEC examinations. The license is the entry ticket. The Microsoft platform does not charge healthcare practices a different rate from commercial banks for the same Microsoft Entra ID Conditional Access policy engine, the same Microsoft Defender threat protection, or the same Microsoft Purview audit log retention.
For a 100-person behavioral health nonprofit that wants the full enterprise security and compliance stack, Microsoft 365 E5 for Nonprofits at $22.80 a user a month bundles Microsoft Defender XDR (Endpoint Plan 2, Identity, Cloud Apps, Office 365 Plan 2), the full Microsoft Purview suite (Audit Premium, Information Protection, DLP, eDiscovery Premium, Insider Risk Management, Communications Compliance), Microsoft Entra ID P2 (Privileged Identity Management, Identity Protection), Microsoft Sentinel-grade telemetry pipelines through Defender XDR, and Power BI Pro. Standalone equivalents would exceed $30 a seat. E5 NP at $22.80 a seat replaces approximately $15-20 of standalone adders.
The license cost is the smaller half of the calculation. The larger half is the configuration, monitoring, and audit-ready evidence work that converts a licensed tenant into a defensible tenant. That work is where a Tier 1 CSP's operating model lives.
Most healthcare 501(c)(3)s qualify for non-profit Microsoft pricing. Few actually claim it.
ABT verifies eligibility, manages the Goodstack validation, provisions the non-profit SKUs through Microsoft Partner Center, and hardens the tenant against HIPAA Security Rule expectations as part of the onboarding. The license discount is the door. The Guardian operating model is the room.
Talk to a Healthcare Specialist Get Your Microsoft Secure ScoreThe July 2026 Deadline Worth Calendaring
Microsoft has announced a non-profit price increase effective July 1, 2026. The increases are modest in absolute terms but compound for any organization that does not lock current pricing before the renewal anniversary moves past that date.
| SKU (Nonprofit) | Current | July 1, 2026 | Change |
|---|---|---|---|
| Microsoft 365 E3 Nonprofit | $9.00 / user / mo | $9.75 / user / mo | +8.3% |
| Microsoft 365 E5 Nonprofit | $22.80 / user / mo | $24.00 / user / mo | +5.3% |
| Microsoft 365 Business Standard Nonprofit | $3.00 / user / mo | $3.50 / user / mo | +16.7% |
| EMS E3 Nonprofit | $2.65 / user / mo | $3.00 / user / mo | +13.2% |
| EMS E5 Nonprofit | $6.56 / user / mo | $7.20 / user / mo | +9.8% |
The practical implication for a healthcare practice is straightforward. Any non-profit quote signed between now and June 30, 2026 should be structured with a renewal anniversary before July 1. That structure locks current pricing through end of June 2027 instead of jumping at the next renewal. For a 100-seat M365 E5 NP deployment, the difference is approximately $1,440 a year in non-profit price protection. For practices considering the move to non-profit pricing, the calendar mechanics matter as much as the eligibility paperwork.
A Note on Microsoft 365 Business Premium Nonprofit
Microsoft 365 Business Premium Nonprofit holds at $5.50 a user a month through the July 1 price increase. For sub-300-staff healthcare orgs, Business Premium plus Microsoft Defender for Office 365 Plan 2 ($2.00 NP) lands at roughly $7.50 a user a month for a credible HIPAA-grade stack. This pricing profile is one of the few that the July 1 schedule does not change.
Guardian for Healthcare: The Operating Model Behind the License
The license is the entry ticket. The configuration and monitoring discipline is the actual security control. ABT's Guardian operating model for healthcare runs four continuous phases against every tenant ABT manages. Each phase maps to a HIPAA Security Rule expectation and to the specific findings OCR has been citing in 2025 settlements.
Hardening
ABT deploys a tenant baseline that turns on multi-factor authentication through Microsoft Entra ID Conditional Access, configures Microsoft Purview audit log retention for the duration HIPAA expects, applies DLP policies that detect protected health identifiers, and enables Microsoft Defender for Office 365 anti-phishing for the email surface that produces most healthcare breaches. The baseline maps directly to the HIPAA Security Rule's required and addressable specifications, and it is the same baseline ABT applies to community bank tenants that pass FFIEC examinations.
Monitoring
Guardian checks tenant health continuously against 160-plus Microsoft Secure Score controls. When a setting drifts from the baseline (someone disables Conditional Access for a vendor account, a new admin account is created without MFA, an external sharing link gets created for a folder labeled PHI), Guardian flags it. The output is the evidence trail OCR expects when it asks for a current, accurate risk analysis. Monitoring runs continuously rather than at quarterly audit checkpoints.
Insights
Guardian Security Insights produces the kind of artifact that a HIPAA risk analysis looks like in 2026: a documented record of what is in the tenant, what is exposed, what is at risk, and what has been remediated. The same evidence supports cyber insurance applications, examiner inquiries, board reporting, and the corrective-action-plan inquiries OCR sends to covered entities after a breach. The insight pack is built to be handed directly to an auditor or attorney; no translation step is required.
Response
When something does fire, Guardian's automated session revocation kicks in. Any risky sign-in event triggers a Microsoft Graph call that immediately kills all refresh tokens across every device and session for the affected identity. For HIPAA practices, that mechanic is the difference between the 279-day median breach detection time IBM tracks and a contained event. Response is automated so that a 24/7 SOC headcount is not the only thing standing between an early signal and a published breach notification.
The pattern we see at clinics under 100 employees is the same pattern we have seen at community banks for two decades. The licenses are in place. The BAA is signed. The tenant is running on the Microsoft defaults. The risk analysis on file is older than 12 months. The single biggest move a healthcare practice can make in any quarter is to verify that what is documented on paper matches what is actually deployed in the tenant. That match-or-mismatch is the question OCR walks in with.
The work is not technically complex for a Tier 1 CSP. The work is operationally consistent. Continuous hardening, continuous monitoring, evidence trail, automated response. Repeated every day across every tenant under management. That consistency is what a small healthcare practice cannot build internally, and it is what a Tier 1 CSP relationship is structurally positioned to deliver at the scale at which a five-person clinic can afford it.
A Tier 1 Microsoft Cloud Solution Provider gives a small healthcare practice the same Microsoft platform foundation a billion-dollar bank uses, at non-profit pricing that lands the HIPAA-grade stack under $200 a month for a typical small clinic, run under a manage-not-host architecture that keeps your patient data inside Microsoft's BAA-covered infrastructure, with an operating model that produces the audit-ready evidence OCR has been demanding in every 2025 settlement. The license is the door. The operating model is the room.
Frequently Asked Questions
Per Microsoft's canonical framing, Cloud Solution Providers manage customer Microsoft 365 tenants rather than host them. ABT manages your tenant via delegated administration: configuration access, not data access. For Azure, the model is different. An Azure subscription is customer-controlled cloud infrastructure that ABT operates as your partner of record, which is the canonical sense of "host." The combined statement: "We manage your Microsoft 365 tenant. We host your Azure environment." The practical consequence for healthcare is that your patient data lives inside your Microsoft 365 tenant under Microsoft's HIPAA Business Associate Agreement, with ABT applying the configuration discipline that makes it HIPAA-ready.
If your organization is a U.S. 501(c)(3) with a community-benefit health mission, you almost certainly qualify. Microsoft's eligibility framework explicitly lists federally qualified health centers, rural health clinics, independent critical access hospitals, skilled nursing facilities, long-term care facilities, and standard 501(c)(3) free clinics and behavioral health nonprofits. Verification runs through Goodstack, Microsoft's third-party validator, and typically completes in about three business days. The October 2025 Microsoft policy change made eligibility content-neutral, so values-based or ideological screening no longer applies. A Tier 1 CSP can verify eligibility, manage the Goodstack process, and provision the non-profit SKUs through Microsoft Partner Center.
A Tier 1 Microsoft Cloud Solution Provider holds a direct partnership with Microsoft (no second-tier distributor between the CSP and the Microsoft commerce platform). The CSP transacts every license, subscription, and Azure subscription with Microsoft directly and accepts the support obligations Microsoft requires of direct partners. The architectural difference matters for healthcare: under the Microsoft delegated admin model, the CSP holds configuration rights on your tenant, not a copy of your data. Traditional managed IT providers often pull mailbox copies, backup repositories, monitoring agent telemetry, and customer credentials into their own infrastructure. The Tier 1 CSP delegated admin model gives you architectural isolation by design: the partner's access is scoped to configuration tasks, and your data stays in your tenant.
For a 25-employee community health center on non-profit pricing, a HIPAA-aligned Microsoft 365 license stack lands at approximately $187 a month. The recipe: Microsoft 365 Business Premium for Nonprofits at $5.50 a seat for the productivity and core security bundle (Outlook, Word, Excel, Teams, SharePoint, OneDrive, plus Microsoft Defender for Business, Microsoft Intune Plan 1, Microsoft Entra ID P1, Microsoft Purview Information Protection P1), Microsoft Defender for Office 365 Plan 2 at $2.00 a seat for upgraded email security, and the $2,000 Azure annual non-profit credit covering ancillary infrastructure. The Microsoft HIPAA Business Associate Agreement is included automatically. The license is the entry ticket; the Guardian operating model around the license is the part that converts a licensed tenant into a defensible tenant.
No. The Microsoft Business Associate Agreement covers Microsoft's responsibilities for the underlying cloud service, including Microsoft 365 and Azure services that handle protected health information. The BAA does not configure your tenant, enforce multi-factor authentication, set DLP policies, retain audit logs, or document your risk analysis. Those responsibilities sit with the covered entity. Microsoft documents the split at learn.microsoft.com under the HIPAA HITECH offering page. A signed BAA plus an unhardened tenant is the configuration the Office for Civil Rights keeps finding when it issues settlements. The BAA is necessary. It is not sufficient. The tenant-side hardening is what closes the gap.
Microsoft has announced a non-profit price increase effective July 1, 2026. Microsoft 365 E3 Nonprofit moves from $9.00 to $9.75 a user a month (+8.3%). Microsoft 365 E5 Nonprofit moves from $22.80 to $24.00 (+5.3%). Microsoft 365 Business Standard Nonprofit moves from $3.00 to $3.50 (+16.7%). Microsoft 365 Business Premium Nonprofit holds at $5.50 (no change). Any non-profit quote signed before June 30, 2026 should be structured with a renewal anniversary before July 1 to lock current pricing through end of June 2027. For practices considering the move to non-profit pricing, the calendar mechanics matter as much as the eligibility paperwork. A Tier 1 CSP can structure the renewal date during provisioning.
Guardian is ABT's operating model for managing Microsoft 365 tenants under HIPAA, FFIEC, GLBA, and similar regulatory regimes. It runs four continuous phases: hardening (a documented tenant baseline with MFA enforcement, Conditional Access policies, Purview audit log retention, DLP for protected health identifiers, Defender for Office 365 anti-phishing), monitoring (continuous checks against 160-plus Microsoft Secure Score controls and drift alerts), insights (an evidence pack built to be handed directly to an auditor, OCR investigator, or examiner), and response (automated session revocation via Microsoft Graph that kills refresh tokens on any risky sign-in event). For healthcare, every phase maps to a HIPAA Security Rule expectation and to the specific findings OCR has been citing in 2025 settlements.
Related Reading for Healthcare Practices
- M365 Guardian for Healthcare: the hardening, monitoring, insights, and response operating model behind HIPAA-aligned Microsoft 365 tenants.
- The $7.42 Million Question: Why Healthcare Is the Costliest Industry to Breach for 14 Years Running: the IBM 2025 breach cost data, the OCR settlement pattern, and the Microsoft 365 governance gap that drives it.
- HIPAA Security Rule 2026: Six Changes That Will Hit Your IT Operations: what the NPRM at 90 FR 800 changes and the 240-day compliance window practices should start working against now.
- Microsoft Dragon Copilot for Small Physician Practices: what ambient clinical documentation looks like inside a HIPAA-ready Microsoft 365 tenant, including the May 2026 price cut and the ROI math for a 5-physician clinic.
- Why a Tier 1 Microsoft CSP Matters (Financial Institutions): the sister article for the banking, credit union, and mortgage book, with the same architecture story applied to FFIEC examination discipline.
- Healthcare Nonprofit Cybersecurity 2026: the October 2025 Microsoft policy change for FQHCs, free clinics, behavioral health, and faith-based health ministries; the July 1, 2026 pricing deadline; and the three-step playbook for mission-driven healthcare 501(c)(3) organizations.

Justin Kirsch
CEO, Access Business Technologies
Justin Kirsch has helped highly regulated organizations harden their Microsoft 365 environments since 1999. As CEO of Access Business Technologies, the largest Tier 1 Microsoft Cloud Solution Provider dedicated to financial services and other regulated industries, he helps more than 750 institutions configure, secure, and monitor the Microsoft cloud against the standards regulators actually inspect against, including HIPAA, FFIEC, GLBA, NCUA, and OCC.