In This Article
- What Interface Security Means for Financial Institution Platforms
- Top Threats Targeting Client-Facing Interfaces
- MFA Done Right: Beyond Push Notifications
- API Security for Core Systems and Third-Party Integrations
- Zero Trust Architecture for Financial Services Platforms
- Encryption and Data Protection Standards
- Compliance Alignment: GLBA, FFIEC, and Multi-Regulator Requirements
- Frequently Asked Questions
Financial services topped the ITRC's 2025 breach list with 739 compromises. The Verizon DBIR found that 22% of breaches still start with stolen credentials. And adversary-in-the-middle attacks surged 146% year over year (Microsoft Digital Defense Report), proving that even MFA isn't the finish line it used to be.
For banks, credit unions, and mortgage companies, the stakes go beyond operational disruption. Client-facing portals collect Social Security numbers, account histories, tax returns, and credit data. A single breach exposes thousands of clients and invites regulatory action from the OCC, FDIC, NCUA, CFPB, and state attorneys general simultaneously.
This guide breaks down how to lock your financial institution's platform interfaces against the threats that matter most right now. No theory. Just the controls that stop attackers and satisfy examiners.
What Interface Security Means for Financial Institution Platforms
Interface security protects every entry point where people or systems touch your platform. That includes client application portals, staff dashboards, third-party API connections, document upload endpoints, and core system integrations.
These interfaces carry the richest data in your organization. A single loan file may contain 40+ pages of financial records. A bank account opening package includes government-issued IDs, employment verification, and beneficial ownership documentation. When an interface is compromised, attackers gain access to everything the client submitted.
Why over-privilege creates most unauthorized access. The 2026 Zero Trust Report found that 56% of organizations cite employee over-privilege as the leading cause of unauthorized access. In financial institution operations, that means loan processors with admin rights they never use, tellers with access to systems beyond their role, and API connections with broader permissions than required. Microsoft Entra Privileged Identity Management addresses this directly through just-in-time, time-limited admin access.
Top Threats Targeting Client-Facing Interfaces
Credential stuffing dominates. Attackers test stolen username-password pairs against your client portal at scale. The success rate sits between 0.2% and 2%, but with billions of attempts, even low conversion rates produce real breaches. Banks, credit unions, and mortgage companies with properly configured Conditional Access policies block these attempts before they reach the authentication layer.
Phishing has evolved. AI-generated phishing emails now achieve a 72% open rate (SQ Magazine, 2025), and 71% of employees admit to risky actions like clicking unknown links or sharing credentials (Proofpoint, 2024). For loan officers handling dozens of emails daily, or bank tellers processing customer requests, one convincing message can compromise an entire operation.
Session hijacking is growing fast. Industry data shows that token theft, stealing session cookies to impersonate authenticated users, has become the primary MFA bypass technique. Microsoft Defender for Cloud Apps detects and blocks these attacks in real time when properly configured.
API abuse rounds out the threat list. Unmonitored endpoints connecting your core banking system or LOS to credit bureaus, verification providers, and pricing engines create pathways attackers exploit without touching the front door.
In 2024, the Marquis Software Solutions breach exposed 672,000 individuals across 74+ banks and credit unions after attackers compromised a shared processing platform. Session-based attacks and credential reuse gave attackers lateral access across institutions sharing the same vendor infrastructure. This is why phishing-resistant MFA (FIDO2 keys, passkeys) and vendor segmentation matter more than any other single control.
Marquis Software Solutions Breach Notification, 2024; Maine Attorney General FilingMFA Done Right: Beyond Push Notifications
Microsoft research confirms that MFA blocks 99.9% of account compromise attempts. But not all MFA works the same. SMS-based codes remain vulnerable to SIM swapping. Push notifications invite fatigue attacks where users approve requests just to stop the buzzing. Microsoft's Digital Defense Report documented a 146% increase in adversary-in-the-middle attacks designed to bypass MFA.
For staff with privileged access. Hardware-bound credentials eliminate phishing risk entirely. Deploy first for IT admins, compliance officers, and anyone with access to core systems.
For client-facing portals and standard staff accounts. Users enter a displayed number rather than tapping "approve," defeating fatigue attacks. Microsoft Authenticator supports this natively.
Enforce MFA based on sign-in risk, device compliance, and location. Approved office workstations get fewer prompts than unknown devices overseas. ABT configures these as part of every Guardian deployment.
Throttle credential stuffing with lockout thresholds that balance security and client experience. Too aggressive locks out legitimate clients. Too lenient lets attackers brute-force their way in.
Only 10% of organizations enforce MFA across all applications. Close that gap on your core banking, LOS, and client portal interfaces first, then extend to every connected service.
"The institutions we see breached aren't the ones without MFA. They're the ones with MFA on the front door but not on the API connections, admin consoles, or backup systems. Attackers go where the controls aren't."
Serving 750+ financial institutions since 1999
Find Your Security Gaps Before Attackers Do
ABT's security assessment identifies which interfaces lack proper controls and prioritizes fixes by risk level.
API Security for Core Systems and Third-Party Integrations
Your client portal connects to credit bureaus, automated underwriting systems, verification services, and core banking platforms through APIs. For mortgage companies, Encompass connects to dozens of third-party services through its partner ecosystem. For banks and credit unions, core systems like Symitar, FIS, and Fiserv connect to payment networks, regulatory reporting tools, and account opening workflows. Each connection is an attack surface.
Weak API Security
- Static API keys shared across environments
- Broad permissions on every token
- No monitoring on endpoint volume
- Inputs passed directly to database
- Quarterly manual log reviews
Strong API Security
- OAuth 2.0 or JWT-based authentication with short-lived tokens
- Least-privilege scopes: a credit-pull API cannot write to loan records
- Rate limiting with real-time alerting on unusual patterns
- Request validation rejects malformed inputs before they reach storage
- API gateway logging with automated anomaly detection
Review third-party API permissions quarterly. Vendors change their systems, and yesterday's reasonable scope may be tomorrow's over-privileged connection. ABT's MortgageExchange platform handles data translation between each system's format while enforcing least-privilege API access at every connection point.

Zero Trust Architecture for Financial Services Platforms
Zero Trust operates on three principles: verify explicitly, use least-privilege access, and assume breach. The 2026 Zero Trust Report reveals a stark gap: 82% of organizations call Zero Trust necessary, but only 17% have fully implemented it.
Verify identity at every access request, not just at login. A session that started on a compliant device should re-verify if the device state changes. Microsoft Entra ID Conditional Access evaluates risk signals continuously.
Separate client-facing systems from internal processing. If an attacker compromises a portal, they should not reach your core banking system, LOS, or document vault. Azure network security groups enforce this separation.
Use Microsoft Intune to verify that devices accessing client data meet security baselines before granting access. Unmanaged devices get read-only access at most.
Replace standing admin privileges with time-limited, approval-based access through Microsoft Entra PIM. Admins get access for the task at hand, and it disappears when the window closes.
Start with your highest-risk interfaces: client portals handling PII and API connections to core systems and credit bureaus. Expand from there.
82% of organizations call Zero Trust necessary. Only 17% have fully implemented it. That 65-point execution gap is where most breaches happen.
Encryption and Data Protection Standards
Transport encryption using TLS 1.3 is the baseline. Every connection between client browsers and your platform, between your platform and third-party APIs, and between application servers and databases must be encrypted in transit.
At rest, use AES-256 encryption for stored client documents, PII, and audit logs. Enable database-level encryption and ensure backup files receive the same protection as live data.
Encrypt SSNs, account numbers, and sensitive identifiers at the field level. Even if an attacker reaches your database, individual fields remain unreadable.
Microsoft Purview prevents client documents from leaving approved channels. Configure policies that match your regulatory requirements for data handling.
A processor needs different data access than a closer, and a teller needs different access than an operations manager. Enforce least-privilege at every level.
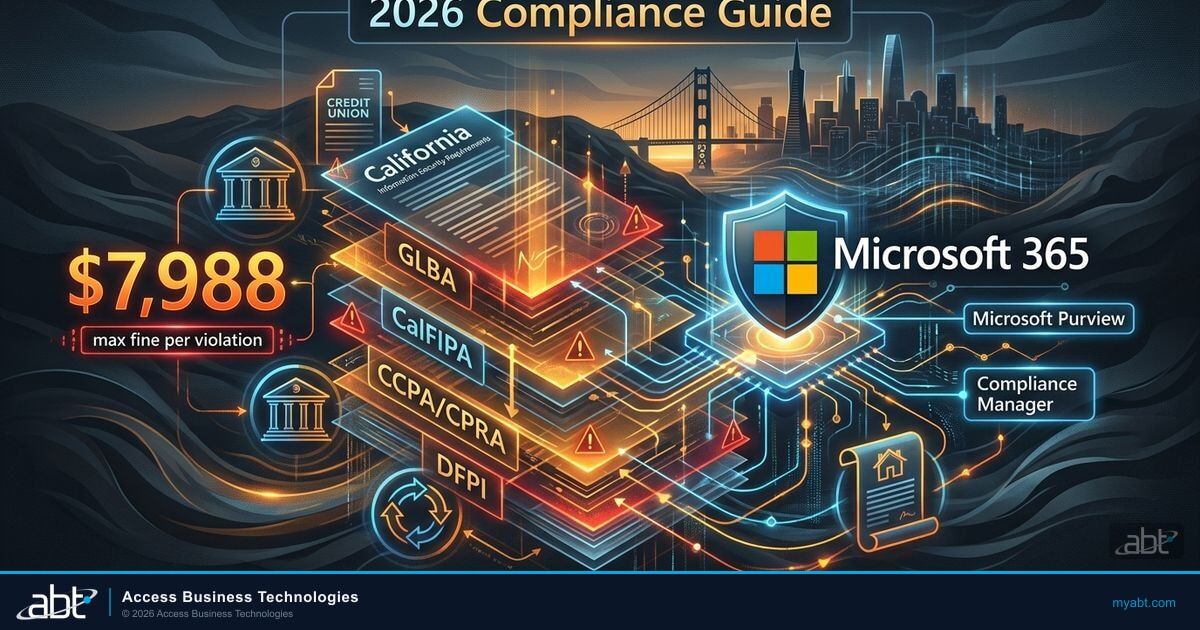
Compliance Alignment: GLBA, FFIEC, and Multi-Regulator Requirements
Interface security is not optional for financial institutions. GLBA requires administrative, technical, and physical safeguards for customer information. The FTC Safeguards Rule updated those requirements with specific technical controls. FFIEC examination procedures evaluate your security architecture against detailed benchmarks.
The regulatory landscape has layers. Banks answer to the OCC or FDIC plus state banking departments. Credit unions answer to the NCUA. Mortgage companies face the CFPB and state licensing authorities. Fannie Mae now requires lenders to report cyber incidents within 36 hours. State regulators from California's DFPI to New York's DFS impose additional cybersecurity mandates.
Build your interface security to the highest standard any regulator applies. That way, you satisfy all of them at once. Log every access event, retain audit data for the period your strictest regulator requires, and keep evidence organized for examiner requests.

ABT secures platform interfaces for 750+ banks, credit unions, and mortgage companies through Microsoft 365, Azure, and Guardian SI. From Conditional Access configuration to API security architecture to MortgageExchange integration security, our team builds security into every connection point so your defenses grow alongside the threats.
Your Interface Security Starts Here
739 financial services breaches in 2025 (ITRC) and a 146% surge in MFA bypass attacks (Microsoft). The question is whether your defenses grow with the threats. ABT's security team identifies your highest-risk interfaces and builds controls that stop attackers and satisfy every regulator that examines your institution.
Frequently Asked Questions
Interface security protects every entry point where clients, staff, and third-party systems interact with your institution's platforms. This includes online banking portals, loan application systems, API connections to core banking and credit bureaus, document upload endpoints, and administrative dashboards. Proper interface security prevents credential theft, unauthorized data access, and compliance violations across all regulators that examine your institution.
Multi-factor authentication requires a second verification step beyond passwords, blocking attackers who possess stolen credentials. Even when login databases are compromised, MFA prevents account access because attackers lack the physical device or biometric factor. Phishing-resistant methods like FIDO2 keys provide the strongest protection against both credential stuffing and real-time phishing attacks targeting banks, credit unions, and mortgage companies.
Financial institutions must comply with GLBA and the FTC Safeguards Rule for customer data protection. FFIEC examination procedures evaluate security architecture in detail. The OCC, FDIC, and NCUA each enforce cybersecurity requirements for their supervised institutions. State regulators including California DFPI and New York DFS impose additional mandates. Fannie Mae requires cyber incident reporting within 36 hours. Meeting all requirements means building to the strictest applicable standard across every regulator that examines your institution.
Zero Trust eliminates implicit trust by verifying every user, device, and connection before granting access. It enforces least-privilege permissions, requires continuous authentication beyond initial login, and segments networks so a breach in one area cannot spread to others. For financial institution platforms, online banking portals, loan processing systems, core banking connections, and API integrations each operate in isolated security zones with independent access controls.

Justin Kirsch
CEO, Access Business Technologies
Justin Kirsch has secured platform interfaces for financial institutions since 1999. As CEO of Access Business Technologies, the largest Tier-1 Microsoft Cloud Solution Provider dedicated to financial services, he leads a team that configures Conditional Access, deploys Zero Trust architecture, and monitors security across Microsoft 365 and Azure environments for more than 750 banks, credit unions, and mortgage companies.