In this article:
- The Problem With Generic MSPs in Financial Services
- Five Ways Generic MSPs Fail Financial Services Clients
- The Real Cost of the Wrong Provider
- What Financial Institutions Should Look For Instead
- How ABT Is Different: Direct-Bill CSP, M365 Guardian, Microsoft Purview
- Frequently Asked Questions
- Technical Reference
Your MSP keeps the lights on. Email works. The Wi-Fi stays connected. When someone forgets their password, they get it reset in a few hours. By most measures, they are doing their job.
Then your examiner arrives. They ask for documentation on your login and access policies, what Microsoft calls Conditional Access. Your MSP does not know what that means. They ask how you are preventing sensitive data from leaving the organization. Your MSP set up antivirus and called it done. They ask about your incident response plan. Your MSP has a generic template they downloaded three years ago.
This is what happens when a financial institution hires a generic MSP. The day-to-day IT works fine. The compliance, security, and regulatory readiness does not exist. And you will not know it until an examiner, an auditor, or an attacker shows you.
In August 2025, Marquis Software Solutions, a fintech company that builds compliance and marketing software for over 700 banks and credit unions, was breached through a supply chain failure. Attackers exploited a vulnerability in SonicWall's cloud backup system to steal Marquis's firewall configuration, then used that access to reach customer data from 80 financial institutions. 824,000 consumers. SSNs, account numbers, taxpayer IDs.
Meanwhile, four regulators tightened MSP and vendor oversight in a five-month span: NYDFS (Oct 2025), CISA CPG 2.0 (Dec 2025), NCUA 2026 priorities (Jan 2026), and the SEC's Regulation S-P 72-hour vendor notification deadline (June 2026).
The Problem With Generic MSPs in Financial Services
Most managed service providers build their business around small and mid-size companies that need email, file sharing, and a help desk. Law firms, accounting practices, medical offices, construction companies. The core service is the same for all of them: set up Microsoft 365, deploy antivirus, manage the network, answer support tickets.
Financial institutions look like those companies from the outside. Same size, same software, same basic IT needs. So the MSP sells them the same package at the same price and assumes they are covered.
The gap shows up in three areas that generic MSPs do not have the expertise to address:
- Regulatory compliance. Banks, credit unions, and mortgage companies operate under multiple regulators: FFIEC, GLBA, NCUA, OCC, and CFPB, plus state-level agencies. Each has specific IT security expectations. A generic MSP has never translated the retired FFIEC Cybersecurity Assessment Tool into its NIST CSF 2.0 successor reference (the FFIEC retired CAT on August 31, 2025), does not understand GLBA Safeguards Rule requirements, and cannot produce the evidence packages examiners expect.
- Data classification and protection. Financial institutions handle data that carries strict regulatory obligations: Social Security numbers, account numbers, credit reports, loan documents, wire transfer details. Generic MSPs treat all data the same. Financial services IT requires Microsoft Purview data classification, DLP rules, sensitivity labels with encryption, and access controls calibrated to the sensitivity of the information.
- Audit readiness. Financial institutions get examined regularly. OCC exams, NCUA exams, state banking department audits, GSE seller/servicer reviews for mortgage companies. Each examiner expects documented IT controls, evidence of testing, and proof that policies are enforced. Generic MSPs do not maintain this documentation because their other clients do not need it.

Five Ways Generic MSPs Fail Financial Services Clients

They Deploy Microsoft 365 Without Configuring It for Compliance
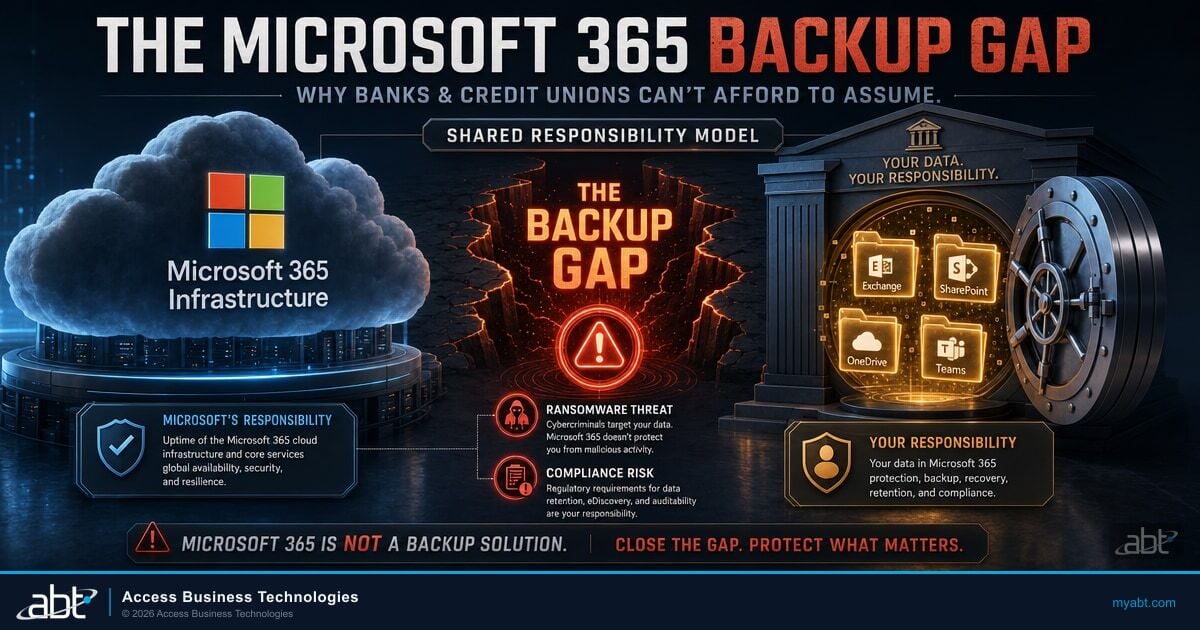
Microsoft 365 ships with powerful security and compliance features: Conditional Access, Microsoft Purview DLP rules, sensitivity labels, information barriers, retention policies, and audit logging. Out of the box, almost none of these are turned on.
A generic MSP sets up mailboxes, configures basic MFA, and moves on. They do not create Conditional Access policies that block legacy authentication or restrict access from non-compliant devices. They do not configure DLP rules that prevent customer account numbers from being emailed to personal Gmail accounts. They do not set up sensitivity labels that automatically encrypt documents containing loan data.
The result: your examiner sees a Microsoft 365 environment with default security settings, and your institution gets findings. Not because you lack the technology, but because nobody configured it for financial services.
They Cannot Map Their Work to Your Regulatory Framework
When your examiner asks how your IT controls align with the FFIEC cybersecurity maturity domains, your MSP should be able to answer. When your auditor asks which GLBA safeguards are implemented at the technical level, your MSP should produce a mapping document.
Generic MSPs work from their own service catalog, not your regulatory framework. They can tell you they installed antivirus on every endpoint. They cannot tell you how that implementation maps to NIST CSF 2.0 Functions (the successor reference the FFIEC directs institutions to after retiring the CAT on August 31, 2025). The gap between "we did IT stuff" and "here is how our IT work satisfies your compliance requirements" is where generic MSPs fail.
Their Security Monitoring Is Passive, Not Active
Most generic MSPs describe their security monitoring as "24/7" because they have a tool that collects logs. Collecting logs and actively monitoring for threats are two different things.
Financial institutions need active threat detection: real-time analysis of unusual sign-in patterns, impossible travel alerts, credential spray detection, and monitoring for unusual file access on sensitive data. A generic MSP's monitoring typically catches obvious things like a server going offline. It does not catch an attacker who stole a loan officer's password and is quietly copying borrower data.
The gap between "we did IT stuff" and "here is how our IT work satisfies your compliance requirements" is where generic MSPs fail.
They Do Not Understand Core System Integrations
Every financial institution runs industry-specific software that generic MSPs have never touched:
- Banks: FIS, Fiserv, Jack Henry, Corelation core banking systems. Online and mobile banking platforms. Wire transfer systems. BSA/AML software.
- Credit unions: Symitar, DNA, Corelation Keystone, CU*BASE. Shared branching networks. CUSO integrations.
- Mortgage companies: Encompass, Byte, LoanSoft loan origination systems. Document management. GSE delivery platforms (Fannie Mae, Freddie Mac).
These systems connect to Microsoft 365, to your network, and to each other. A misconfigured firewall rule can break wire transfers. A botched patch can take down your loan origination system. Generic MSPs approach these systems cautiously at best and dangerously at worst, because they do not understand what they do or how they connect.
Their Incident Response Plan Does Not Account for Regulatory Requirements
When a financial institution experiences a security incident, the response has dimensions that do not exist in other industries:
- Regulatory notification timelines (OCC requires notification within 36 hours for certain incidents)
- Suspicious Activity Report (SAR) filing coordination if the incident involves potential fraud
- Board notification requirements
- Customer notification procedures under state breach notification laws plus federal banking regulations
- Evidence preservation for potential law enforcement involvement and examiner review
A generic MSP's incident response plan says "contain, eradicate, recover, notify." A financial services plan specifies who gets notified at which regulator, in what order, within what timeframe, and what documentation must be preserved.

Consider what happened with Marquis Software Solutions. Banks shared customer data with Marquis for regulatory reporting and marketing analytics. Standard practice with a trusted vendor. Attackers exploited a flaw in SonicWall's cloud backup system to steal Marquis's firewall configuration, then used those credentials to breach Marquis's network. 80 financial institutions. 824,000 consumers, and it took four months before those institutions were notified.
Under the SEC's updated Regulation S-P, which takes full effect for smaller financial institutions in June 2026, service providers must notify institutions within 72 hours. Not four months. If a specialized vendor's supply chain can fail this badly, a generic MSP with commodity tools, shared infrastructure, and no regulatory awareness has no chance of meeting that standard when their turn comes.
The Real Cost of the Wrong Provider
The cost of a generic MSP is not the monthly invoice. It is what happens when the gaps they do not cover become problems:
- Examination findings. Regulatory findings require formal remediation plans, consume management attention, and can trigger increased examination frequency. Multiple findings in the same area can escalate to enforcement actions.
- Breach response costs. Financial services data breaches cost more than breaches in other industries because of regulatory fines, customer notification requirements, credit monitoring obligations, and the reputational damage that drives depositors or borrowers to competitors.
- Audit preparation scrambles. When your examiner gives you 30 days' notice and your MSP cannot produce compliance documentation, your internal team spends weeks manually assembling evidence.
- Vendor risk management gaps. Your MSP is a critical third-party vendor. If they do not have a SOC 2 Type II report, your examiner will flag that gap.
- Insurance claim denials. If your MSP deploys MFA on most accounts but not all, or keeps security logs for 30 days instead of the 90 that insurers now require, your institution may be paying premiums for coverage that will not pay out.
What Financial Institutions Should Look For Instead
The difference between a generic MSP and a financial services IT provider comes down to five things:
- Regulatory fluency. Ask them to describe how they would help you prepare for your next FFIEC cybersecurity assessment or NCUA IT exam. If they cannot answer specifically, they have not done it.
- SOC 2 Type II attestation. Not Type I. Type II means an independent auditor verified their controls work over a sustained period.
- Core system experience. Ask which core banking, credit union, or loan origination systems they have worked with. Names, not generalities.
- Compliance documentation. A qualified provider maintains ongoing compliance evidence, not scrambling to create it when your examiner asks.
- Financial services client base. How many banks, credit unions, or mortgage companies do they serve? If you would be their first, you are paying for their learning curve.

How ABT Is Different: Direct-Bill CSP, M365 Guardian, Microsoft Purview
ABT has served thousands of financial institutions since 1999 and currently manages Microsoft 365 tenants for more than 750 banks, credit unions, mortgage companies, and securities firms. The company was built specifically for regulated industries, not retrofitted for them. Two structural advantages separate ABT from the generic MSP pattern this article describes, and both are advantages a generic shop cannot replicate with effort or salesmanship.
Microsoft Direct-Bill CSP, not a reseller layer. ABT is a Tier-1 Microsoft Cloud Solution Provider that transacts directly with Microsoft and holds delegated administrative privileges (GDAP) against every customer tenant in its footprint. A generic MSP almost always sits one or two tiers below that as an indirect reseller, which means they sell Microsoft licenses through a distributor and have no scoped technical relationship with the tenants they support. The practical difference shows up the first time something breaks at the platform level: a Direct-Bill CSP has named Microsoft engineers on the line, while an indirect reseller opens a ticket against a distributor's queue and waits. The difference also shows up under amended SEC Regulation S-P and the FFIEC IT Examination Handbook's vendor-management expectations, where the delegated-admin relationship is precisely the evidence examiners look for to prove that the partner has scoped, documented access rather than a shared admin account left over from initial setup. ABT's GDAP grants are scoped per role, renewed on a published cadence, and produced as evidence in the firm's vendor oversight file. For more on what ABT's CSP role actually covers, see our companion article on what to look for in a financial services IT provider.
M365 Guardian plus Microsoft Purview is the operating model, not just a license bundle. The Microsoft 365 controls that examiners grade against, Conditional Access in Microsoft Entra ID, Microsoft Defender for Office 365 and Defender for Endpoint, Microsoft Intune device compliance, Microsoft Sentinel as the SIEM, and Microsoft Purview Audit, DLP, sensitivity labels, retention policies, and Communication Compliance, all ship inside reasonably licensed M365 tenants. The problem in the generic-MSP pattern is not the absence of the controls. It is the absence of an operating model that applies them consistently across every tenant, monitors them for drift, and produces audit evidence on demand in the form an examiner accepts. ABT's M365 Guardian is that operating model for financial services. Guardian applies financial-services-tuned configurations, layers Microsoft Purview audit retention extended to the SEA Rule 17a-4 and FFIEC retention floor, binds Purview DLP rules to customer NPI and core-banking data flows, and produces the cross-tenant evidence packages a CCO can hand to an examiner in two hours rather than three weeks. The free Microsoft 365 Security Assessment grades your current tenant against the same 80-policy financial-institution baseline ABT applies on day one. For deeper context on how this maps to the FFIEC examiner playbook, see our guide on FFIEC assessment requirements.
- Tier-1 Microsoft Direct-Bill CSP. Delegated admin under GDAP, named Microsoft engineering support, and the partner-of-record relationship examiners expect to see in your vendor oversight file.
- M365 Guardian operating model. Continuous monitoring of Microsoft 365 environments against more than 100 security benchmarks calibrated for financial services, with findings mapped to FFIEC, GLBA, and NCUA terms rather than vendor jargon.
- Microsoft Purview as the audit-evidence layer. Audit retention, DLP, sensitivity labels, and Communication Compliance configured against the actual books-and-records rules that apply to banks, credit unions, mortgage companies, and broker-dealers.
- Independent SOC attestation. ABT is independently audited under SOC 1 Type 2 (which includes a dedicated security-controls section) and SOC 2 Type 1 attestation reports, with a SOC 2 Type 2 examination ongoing. That third-party verification is the evidence your examiner expects to see in your vendor risk management file.
- 750+ financial-institution footprint. Hundreds of regulatory examinations across banks, credit unions, and mortgage companies. ABT's team knows what examiners look for because they have helped institutions prepare for over 25 years.
The right IT provider for a financial institution is not the one with the lowest monthly invoice. It is the one who can sit next to you during your next regulatory examination and explain, in your examiner's language, exactly how every IT control maps to your compliance requirements. A Tier-1 Microsoft Direct-Bill CSP that manages Microsoft 365 tenants under delegated admin, layers M365 Guardian as the operating model, and uses Microsoft Purview to produce the audit evidence is the structural answer to that question.
Get a Financial-Services MSP Readiness Review
ABT runs the Microsoft Direct-Bill CSP model, M365 Guardian operating layer, and Microsoft Purview audit-evidence stack described in this article for more than 750 banks, credit unions, mortgage companies, and broker-dealers. A 30-minute conversation maps your current Microsoft 365 tenant, surfaces the gaps your next examiner is most likely to find, and outlines what an ABT-managed deployment would cover. No commitment, no quote, no obligation.
Frequently Asked Questions
Generic MSPs fail at financial services compliance because they build their services around general business IT needs, not regulatory requirements. They deploy Microsoft 365 with default security settings, lack experience translating the retired FFIEC Cybersecurity Assessment Tool into NIST CSF 2.0 (the successor reference since August 2025), cannot produce the compliance documentation examiners require, and have no experience with core banking platforms or loan origination software.
An MSP serving financial institutions should hold SOC 2 Type II attestation at minimum, verifying their security controls work over a sustained period. Additional qualifications include Microsoft Tier-1 Direct-Bill Cloud Solution Provider credentials with delegated administrative access under GDAP, FFIEC cybersecurity assessment experience, GLBA Safeguards Rule familiarity, and incident response and business continuity plans meeting examiner standards.
Ask your current MSP three questions: Can you show me your SOC 2 Type II report? Can you describe how our IT controls map to the FFIEC cybersecurity maturity domains? Can you produce our compliance evidence package within 24 hours if our examiner requests it? If they cannot answer yes to all three, they are not operating at the level a financial institution requires.
A generic MSP provides standard IT management including email, help desk, antivirus, and network management. A financial services IT provider adds regulatory compliance support (FFIEC, GLBA, NCUA, OCC), configures Microsoft 365 for financial services security with Microsoft Purview and Conditional Access, maintains compliance documentation for examiners, understands core banking integrations, and carries certifications like SOC 2 Type II.
Some financial institutions split IT management between a local provider for hardware and on-site support and a specialized provider for security, compliance, and Microsoft 365 management. This can work if responsibilities are clearly documented and both providers coordinate on security policies. However, it introduces vendor management complexity, creates accountability gaps when security responsibilities overlap, and requires managing two vendor relationships for examiner reporting.
For FFIEC and GLBA compliance, an MSP should configure Conditional Access policies in Microsoft Entra ID to enforce login restrictions and device compliance, Microsoft Purview Data Loss Prevention (DLP) rules to prevent sensitive financial data from leaving the organization, Microsoft Purview sensitivity labels to classify and encrypt documents containing borrower PII or account data, DMARC email authentication to prevent domain spoofing, Microsoft Purview retention policies matching regulatory record-keeping requirements, and Purview Audit logging for examiner evidence packages. These features ship with Microsoft 365 but require financial services-specific configuration.
Four major regulatory actions tightened MSP and vendor oversight between October 2025 and June 2026. NYDFS issued guidance naming IT managed services as high-risk third-party providers. CISA CPG 2.0 explicitly calls out managed service providers as a risk category. NCUA 2026 supervisory priorities direct examiners to assess vendor management practices. The SEC Regulation S-P amendments require service providers to notify financial institutions within 72 hours of detecting a breach, with full compliance required by June 2026.
Technical Reference
Definitions for the regulatory frameworks and technical terms used throughout this article. These are the exact terms your examiner, auditor, or insurance carrier will use.
Regulatory Frameworks
| Framework | Full Name | Applies To |
|---|---|---|
| FFIEC | Federal Financial Institutions Examination Council | Banks, credit unions, thrifts |
| FFIEC CAT | FFIEC Cybersecurity Assessment Tool (retired August 31, 2025) | Prior self-assessment tool for financial institutions; FFIEC now points institutions to NIST CSF 2.0 as the successor reference. |
| GLBA | Gramm-Leach-Bliley Act | All financial institutions handling consumer data |
| FTC Safeguards | FTC Standards for Safeguarding Customer Information | Non-bank FIs including mortgage companies |
| NCUA | National Credit Union Administration | Federally insured credit unions |
| OCC | Office of the Comptroller of the Currency | National banks and federal savings associations |
| CFPB | Consumer Financial Protection Bureau | Consumer lending, mortgages, credit |
Glossary
| Term | Definition |
|---|---|
| BSA/AML | Bank Secrecy Act / Anti-Money Laundering. Federal requirements for detecting and reporting suspicious financial activity. |
| Conditional Access | Microsoft 365 feature in Microsoft Entra ID that controls who can sign in, from which devices, and under what conditions. |
| Credential spray | An automated attack that tries common passwords across many accounts simultaneously, avoiding lockout thresholds. |
| CUSO | Credit Union Service Organization. A company providing specialized services to credit unions. |
| DMARC | Domain-based Message Authentication, Reporting, and Conformance. Prevents spoofing of your domain. |
| DLP | Data Loss Prevention. Microsoft Purview policies that detect and prevent sensitive data from being shared externally. |
| GDAP | Granular Delegated Administrative Privileges. Microsoft's recommended scoped-access model for a Cloud Solution Provider to manage a customer tenant per role and per time window. |
| GSE | Government-Sponsored Enterprise. In mortgage lending, primarily Fannie Mae and Freddie Mac. |
| Impossible travel | Alert triggered when an account logs in from two distant locations within an impossible travel window. |
| LOS | Loan Origination System. Software managing the mortgage application process. Examples: Encompass, Byte, LoanSoft. |
| MFA | Multi-Factor Authentication. Requiring two or more verification methods to sign in. |
| MSP | Managed Service Provider. A company managing IT infrastructure and support on behalf of a client. |
| Microsoft Purview | Microsoft 365's data governance, compliance, and audit suite. Includes Audit, DLP, Information Protection / sensitivity labels, retention, eDiscovery, and Communication Compliance. |
| SAR | Suspicious Activity Report. Required filing when a financial institution detects potential fraud. |
| Sensitivity labels | Microsoft Purview Information Protection feature classifying and protecting documents based on content sensitivity. |
| SOC 2 Type II | Independent audit verifying a provider's security controls work over a sustained period (6-12 months). |
| Tier-1 Direct-Bill CSP | Microsoft's top Cloud Solution Provider program tier. The partner transacts directly with Microsoft, holds named engineering support, and is operationally accountable to Microsoft for how customer tenants are configured. |

Justin Kirsch
CEO, Access Business Technologies
Justin Kirsch has guided Microsoft 365 deployments for regulated financial institutions since 1999. As CEO of Access Business Technologies, the largest Tier-1 Microsoft Cloud Solution Provider dedicated to financial services, he helps more than 750 banks, credit unions, mortgage companies, and securities firms standardize their Microsoft 365 tenants for examination readiness without slowing down how the business actually works.