In this article:
In February 2026, Marquis Software Solutions filed a federal lawsuit against SonicWall. Marquis builds compliance software for over 700 banks and credit unions. In August 2025, attackers breached Marquis through a vulnerability that SonicWall introduced into its own cloud backup system. The firewall was patched. MFA was enabled. None of it mattered. Eighty financial institutions affected. Over 824,000 consumers exposed.
According to the NCUA's own data, 73 percent of credit union cyber incidents trace back to third-party vendors. And the NCUA's response to that number? Six rounds of deregulation proposals in 11 weeks including pulling cybersecurity guidance out of the Code of Federal Regulations and removing the requirement for written vendor contracts.
The National Credit Union Administration (NCUA), the federal agency that regulates and insures credit unions, has pushed these six rounds of deregulation proposals since December 2025. Longer examination cycles. Shorter document request lists. The Financial Crimes Enforcement Network (FinCEN) just dropped redundant beneficial ownership verification for credit union business accounts. Credit union leaders are treating it as good news.
But deregulation doesn't mean what a lot of credit unions think it means for their cybersecurity programs. NCUA cybersecurity requirements in 2026 aren't getting lighter, they're getting harder to satisfy. "Risk-based" means the regulator is trusting your institution to manage risk on your own. That's not less oversight. That's different oversight. And it actually raises the bar for how you demonstrate your cybersecurity posture.
The cybersecurity obligations underneath the NCUA's examination process haven't changed at all. The NIST Cybersecurity Framework (CSF) 2.0 still defines the Identify, Protect, Detect, Respond, Recover, and Govern functions every credit union is expected to implement. The Federal Financial Institutions Examination Council (FFIEC) Information Security and Architecture, Infrastructure and Operations booklets still set the technical expectations. Gramm-Leach-Bliley still requires written information security programs with administrative, technical, and physical safeguards. None of that vanished when NCUA shortened its document request list. The controls that satisfy those obligations on a Microsoft 365 tenant are the same controls examiners expected last year: Microsoft Entra ID Conditional Access enforcing MFA on every sign-in, Microsoft Defender for Office 365 and Defender for Endpoint producing the detection and incident-response signal, and Microsoft Purview Audit Premium plus retention policies producing the time-stamped evidence trail. What changed is who has to prove those controls are configured, monitored, and documented. That responsibility moved off the examiner's checklist and onto your institution.
What NCUA Has Actually Changed About Cybersecurity Requirements in 2026
Here's what's shifted in the regulatory landscape for credit unions as of early 2026: For more details, see our guide on cybersecurity beyond the basics.
- Reduced standard document request lists. Starting January 2026, the standard document request list for risk-focused examinations got shorter. Fewer documents up front, more targeted follow-up based on the examiner's risk assessment.
- Longer examination cycles for eligible credit unions. Institutions that meet certain criteria can qualify for extended periods between full-scope examinations. NCUA is moving away from rigid schedules toward risk-proportionate cycles.
- FinCEN beneficial ownership relief. In February 2026, FinCEN issued an exceptive order eliminating redundant beneficial ownership verification for repeat business customers at credit unions. This removes a specific paperwork burden that duplicated existing checks.
- Five rounds of deregulation proposals under Executive Order 14192. NCUA has systematically reviewed regulations to identify and reduce burden. Each round targets specific rules for elimination, modification, or modernization.
- OCC moving in the same direction for banks. The Office of the Comptroller of the Currency (OCC) is shifting away from fixed examination requirements toward risk-based approaches. This isn't credit union-specific, banks and mortgage lenders regulated under the Federal Financial Institutions Examination Council (FFIEC) framework are seeing the same shift. The entire regulatory model for financial institutions is evolving.
All of this is real, and most of it is welcome. The question is what it means for your cybersecurity program specifically.
Why This Matters Right Now
NCUA's shift from prescriptive to risk-based examination isn't a future plan, it's happening now. Credit unions that relied on checking boxes to pass exams are finding that the new model demands they actually demonstrate how they identified risks and built controls. The regulatory bar didn't lower; it changed shape.

Risk-Based Examination Requires Risk-Based Security
Proving your security decisions are appropriate for your risk profile starts with knowing exactly where you stand today.
Why Risk-Based Examination Raises the Bar
Under a prescriptive model, the examiner tells you exactly what to produce. Check the boxes, hand over the documents, pass the exam. It's rigid, but it's clear. You know exactly what's expected because the regulator spelled it out. For more details, see our guide on what NCUA examiners look for.
Under a risk-based model, the examiner expects you to have defined your own risks, built controls around them, and produced evidence that those controls are working. The conversation shifts from "show me this specific document" to "show me how you identified this risk and what you did about it."
That's a harder conversation. Especially on the technology side.
Under a risk-based model, the examiner expects you to have defined your own risks, built controls around them, and produced evidence that those controls are working.
Prescriptive Model (Legacy)
- Fixed document request list
- Same checklist for every institution
- Pass/fail based on documents produced
- Rigid examination schedule
- Compliance = checking boxes
Risk-Based Model (2026+)
- Targeted follow-up based on risk assessment
- Controls must match your specific risk profile
- Examiner evaluates your risk analysis process
- Cycles proportionate to institutional risk
- Compliance = demonstrating risk awareness
Your Controls Need to Match Your Risk Profile
If your IT environment is managed by a provider who runs the same playbook for every client, the same security template, same monitoring rules, same reports for a credit union as for a dental office, that approach breaks down under risk-based examination. The examiner will ask why your controls look identical to a non-financial business when your risk profile is fundamentally different.
Risk-based regulation rewards institutions that can demonstrate they actually thought about their specific threats and built defenses accordingly. It punishes institutions that were following the checklist only because the checklist was the exam.
Documentation Requirements Don't Shrink
Shorter document request lists don't mean less documentation overall. They mean the examiner is being more selective about what they ask for up front. The expectation is that you maintain comprehensive documentation whether they ask for it or not. When they do ask a follow-up question, you need to produce the answer quickly and with specificity.
Your NCUA examination preparation actually gets more complex under this model, not less. Meeting NCUA cybersecurity requirements now means being ready for any risk-based question the examiner might ask about your program, not just the ones on a predictable document request list.
The Credit Union Breach Backdrop
NCUA's shift to risk-based examination is happening against a backdrop of credit union breaches, dozens of institutions across multiple states. Several connected to the Marquis Software supply chain breach that hit 80 financial institutions and exposed data on over 823,000 consumers.
NCUA is loosening the regulatory framework at the exact moment the threat landscape is intensifying. That's not contradictory. It's the regulator saying: we trust you to handle this. Prove it.
The credit unions that will thrive under this model are the ones that invested in real security controls, real monitoring, and real documentation before the examiner showed up. The ones that were only maintaining compliance because the examiner told them exactly what to maintain are about to find out what "risk-based" really means.
What Smart Credit Unions Are Doing Now
The credit unions we work with aren't treating deregulation as a reason to pull back on security spending. They're treating it as a signal to level up.
Hardening Microsoft 365 Against Specific Threats
Not default templates. Login and device policies, what Microsoft calls Conditional Access, configured for credit union-specific risk scenarios. Data protection rules (Data Loss Prevention, or DLP) that know what member data looks like. Email authentication protocols that prevent attackers from spoofing your credit union's domain (SPF, DKIM, and DMARC) enforced at the domain level, not just enabled. Sensitivity labels applied to member data categories, Social Security numbers, account numbers, loan documents, that match your data classification policy.
Running Continuous Compliance Monitoring
Compliance drift is the silent killer under a risk-based model. You pass your exam in January. Your IT provider makes a change in March, maybe they adjust a Conditional Access policy because a user was having trouble signing in. By the time your next exam rolls around, you've drifted out of compliance and nobody flagged it.
Continuous monitoring catches drift the week it happens, not six months later during an examination. That's the difference between "we maintain compliance" and "we were compliant when the examiner was here."
Building Documentation That Demonstrates Risk-Based Thinking
When your examiner asks "walk me through your approach to vendor risk management," you want an answer that shows you evaluated your specific vendor relationships, identified the risk each one introduces, and built controls proportionate to that risk. Not a templated response about antivirus and firewalls.
The documentation that satisfies a risk-based examiner is different from the documentation that satisfies a checklist examiner. It requires evidence of analysis, not just evidence of compliance.

Why Generic IT Providers Break Down Under This Model
A generic managed service provider builds one security template and applies it to every client. Dental offices, law firms, credit unions: same Conditional Access policy, same monitoring rules, same reports.
Under a prescriptive examination model, that could work. The checklist was the checklist, and if the boxes were checked, you passed.
Under a risk-based model, the examiner asks why your security controls look the same as a business with a completely different risk profile. They ask how you determined that this specific set of controls addresses your specific risks. They ask for evidence that your IT provider understood the credit union threat landscape and configured your environment accordingly.
Your IT provider needs to understand the difference between a credit union's risk profile and a generic small business risk profile. That understanding shows up in the configuration, the monitoring rules, the documentation, and the way they talk to your examiner.
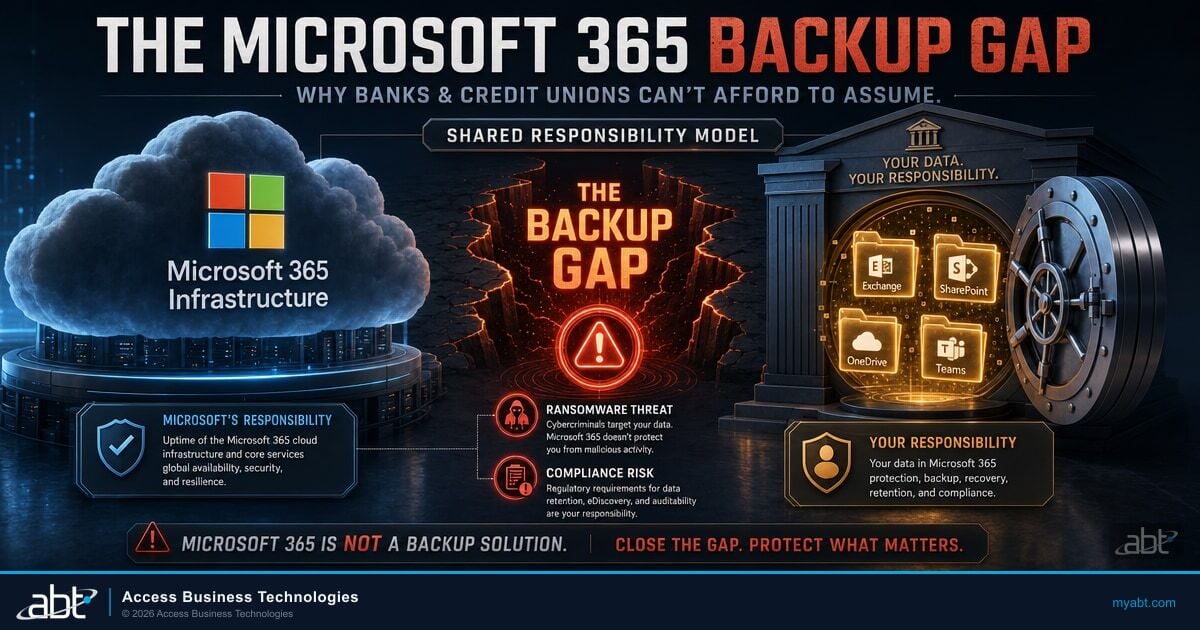
The operating model Access Business Technologies built for that gap is called M365 Guardian. It is how ABT productizes the cybersecurity obligations layer on Microsoft 365 for 750+ banks, credit unions, mortgage companies, and securities firms. ABT manages the Microsoft 365 tenants under delegated admin, applies a financial-services security baseline through Microsoft Entra ID Conditional Access, Microsoft Intune, Microsoft Defender, and Microsoft Purview, monitors the configuration continuously so drift is caught the week it happens, and produces the audit evidence packages an NCUA examiner can accept on demand. The credit union retains its tenant ownership and its regulatory relationships. What it adds is an operational owner that runs the NIST CSF, FFIEC, and GLBA control surface every day of the year, not the four weeks before an examination. That is what makes a Guardian-managed credit union ready for risk-based oversight without the institution needing to rebuild its IT department.
The Bottom Line
NCUA deregulation is real, but it doesn't mean cybersecurity obligations are shrinking. Risk-based examination raises the bar, credit unions must demonstrate they independently identified risks, built proportionate controls, and can produce evidence on demand. The institutions that thrive will be the ones that treated compliance as a minimum, not a ceiling.
institutions since 1999
Deregulation Doesn't Mean Lower Standards
Risk-based examination means examiners expect you to demonstrate why your security decisions are appropriate for your risk profile, not just check boxes.
Frequently Asked Questions
NCUA deregulation reduces specific regulatory requirements through shorter document request lists and longer examination cycles for eligible credit unions. However, cybersecurity obligations remain because NCUA is shifting to risk-based examination. This means credit unions must demonstrate they independently identified risks and built appropriate controls, rather than simply following a prescribed checklist.
Prescriptive examination tells institutions exactly which documents to produce and which controls to implement. Risk-based examination expects institutions to define their own risks, build proportionate controls, and produce evidence those controls work. The examiner evaluates your risk analysis process and control rationale, not just whether specific boxes are checked.
No. NCUA deregulation reduces administrative burden but does not reduce cybersecurity expectations. Risk-based examination actually increases the standard for cybersecurity documentation and control specificity. Credit unions that reduce security investment based on deregulation may face examination findings when examiners evaluate whether their controls match their actual risk profile.
Compliance drift occurs when configuration changes gradually move a credit union out of its approved security baseline between examinations. A Conditional Access policy adjusted for user convenience or a monitoring rule disabled for troubleshooting can create gaps that go undetected until the next exam. Continuous compliance monitoring catches drift when it happens rather than months later.
Credit unions should document their specific risk assessment methodology, ensure security controls are tailored to their risk profile rather than generic templates, implement continuous compliance monitoring for configuration drift, and maintain evidence that their IT environment reflects deliberate risk-based decisions. Working with a managed IT provider experienced in credit union examinations accelerates this preparation.
Credit unions need Conditional Access policies that enforce device compliance, block legacy authentication, restrict access from unmanaged devices, and require multi-factor authentication for privileged accounts. DLP (Data Loss Prevention) rules should detect and block sharing of member PII including Social Security numbers, account numbers, and loan data outside the organization. Additional configurations include DMARC email authentication, sensitivity labels for document classification, and audit logging sufficient to produce evidence packages for NCUA examiners.
Technical Reference
This section defines the regulatory and technical terms used throughout this article. These are the exact terms your NCUA examiner or IT auditor will reference.
Regulatory Terms
| Term | Definition |
|---|---|
| NCUA | National Credit Union Administration. The independent federal agency that regulates, charters, and supervises federal credit unions and insures deposits at federally insured credit unions. |
| FFIEC | Federal Financial Institutions Examination Council. An interagency body that sets uniform standards for examining financial institutions, including the Cybersecurity Assessment Tool (CAT). |
| OCC | Office of the Comptroller of the Currency. Regulates national banks and federal savings associations. Moving toward the same risk-based examination model as NCUA. |
| FinCEN | Financial Crimes Enforcement Network. The U.S. Treasury bureau that combats money laundering and financial crimes. Issues beneficial ownership and anti-money laundering rules. |
| Executive Order 14192 | The federal directive that triggered NCUA's five rounds of deregulation proposals, requiring agencies to review regulations for unnecessary burden. |
| Risk-based examination | An examination approach where the regulator evaluates whether the institution has identified its own risks and built proportionate controls, rather than checking a fixed list of prescribed requirements. |
Technical Terms
| Term | Definition |
|---|---|
| Compliance drift | Gradual movement away from an approved security baseline due to configuration changes made between examinations. Often caused by IT adjustments for user convenience that inadvertently weaken security controls. |
| Conditional Access | Microsoft 365 feature that controls who can sign in, from which devices, and under what conditions. Used to enforce login policies, device compliance, and location-based access restrictions. |
| DLP | Data Loss Prevention. Microsoft 365 policies that detect and prevent sensitive data (member account numbers, SSNs, loan documents) from being shared outside the organization. |
| DMARC | Domain-based Message Authentication, Reporting, and Conformance. An email security protocol that prevents attackers from spoofing your credit union's email domain. |
| Sensitivity labels | Microsoft 365 feature that classifies and protects documents and emails based on data sensitivity. Can automatically encrypt files containing member PII or restrict sharing based on content type. |
| SPF / DKIM | Sender Policy Framework and DomainKeys Identified Mail. Email authentication protocols that work alongside DMARC to verify that emails claiming to come from your domain are legitimate. |

Justin Kirsch
CEO, Access Business Technologies
Justin Kirsch founded ABT in 1999, and his team works with hundreds of credit unions on cybersecurity and IT compliance, giving ABT a front-row seat to how regulatory shifts play out in practice. With an MBA in technology management from CSU Sacramento and 25+ years in financial services IT, he built ABT to help institutions maintain security programs that hold up whether examiners tighten the rules or loosen them.