In This Article
- Why Device Compliance Is a Board-Level Concern
- What Microsoft Intune Device Compliance Actually Does
- Building a Risk-Based Intune Policy: The Executive Playbook
- What Changed in 2026: Intune's Expanding Capabilities
- The Microsoft 365 Security Ecosystem: Intune Doesn't Work Alone
- Implementation Realities: What Financial Institutions Actually Face
- Why Professional Implementation Changes the Equation
- The Bottom Line for Financial Institution Leaders
- Frequently Asked Questions
A loan officer's personal laptop gets stolen at an airport. A credit union teller plugs a personal USB drive into a branch workstation. A bank executive checks email from an unpatched tablet at a hotel. Each of these scenarios happens every week across financial services, and each one represents an endpoint your organization either controls or doesn't.
The uncomfortable math: 46% of compromised systems in credential breaches trace back to unmanaged devices. That number alone should end the debate over whether endpoint management belongs on the board agenda. It does.
Microsoft Intune device compliance is how you close that gap inside the Microsoft 365 ecosystem. Not as an afterthought. As the enforcement layer that determines which devices touch your data and which ones get stopped at the door.
Why Device Compliance Is a Board-Level Concern
Endpoint security used to live in the IT department's backlog. That era ended when regulators, cyber insurers, and auditors started asking specific questions about device posture.
Here's what changed:
- Regulatory pressure is concrete. FFIEC examiners expect documented endpoint controls. NCUA auditors ask credit unions how they manage mobile devices. State regulators want evidence that devices accessing borrower data meet encryption baselines. NYDFS finalized its latest cybersecurity requirements in November 2025, adding strict access controls, complete asset inventories, and universal MFA coverage to its examination checklist. A verbal assurance that "we have policies" no longer satisfies anyone.
- Cyber insurance underwriters check device management. Carriers now ask whether you enforce BitLocker encryption, require minimum OS versions, and block jailbroken devices. Gaps in device compliance translate directly to higher premiums or denied claims.
- Breach costs punish the unprepared. Organizations without Zero Trust controls pay 38% more per breach on average. For a financial institution handling nonpublic personal information, a single unmanaged laptop can turn a $3M incident into a $5M one. For deeper context on how unmanaged endpoints undermine your security investment, see our companion article on the Zero Trust blind spot.
The question for CIOs and CISOs isn't whether to enforce device compliance. It's how quickly you can get there without disrupting operations.
What Microsoft Intune Device Compliance Actually Does
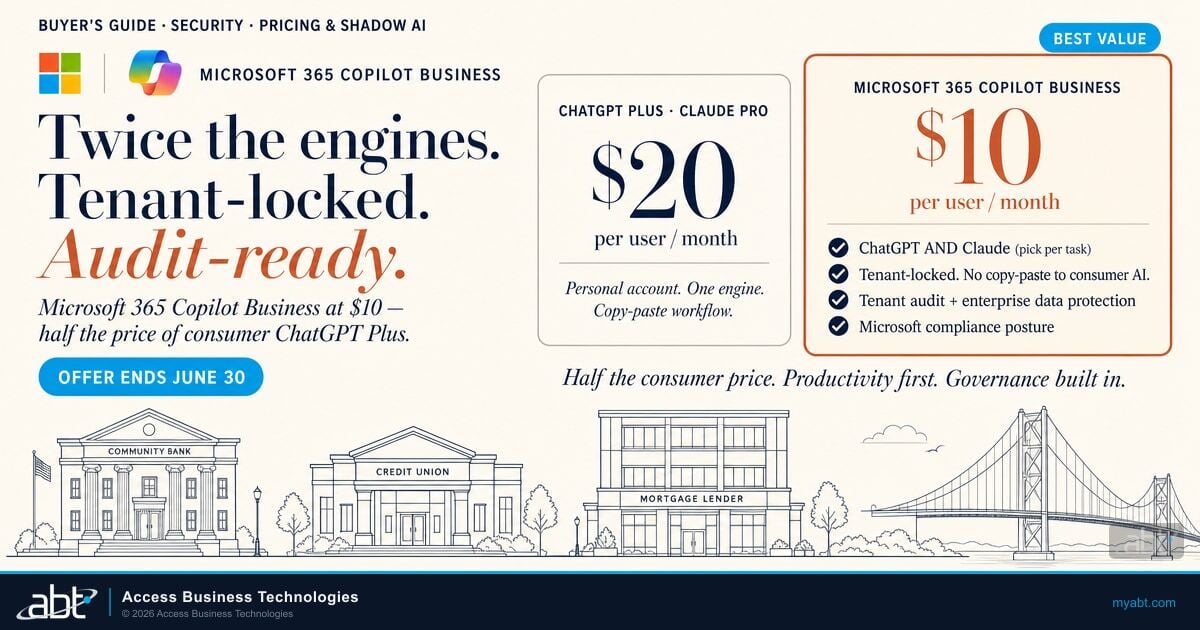
Intune is Microsoft's cloud-based endpoint management platform, included in Microsoft 365 Business Premium and Enterprise E3/E5 licenses. It handles two jobs: Mobile Device Management (MDM) for company-owned hardware and Mobile Application Management (MAM) for personal devices.
An Intune compliance policy defines what a healthy device looks like. Think of it as a health check that runs continuously, not just at enrollment. Devices that pass get marked "compliant." Devices that fail get flagged and can be blocked from accessing corporate resources.
Baseline compliance checks include:
- BitLocker encryption: Is the hard drive encrypted? For any device handling NPI, this is non-negotiable.
- OS version: Is the operating system current and receiving security patches?
- Password/PIN strength: Does the device require a PIN, password, or biometric unlock that meets your policy?
- Jailbreak/root detection: Has the device been tampered with in ways that bypass built-in security?
- Threat level: When integrated with Defender for Endpoint, Intune can assess the device's active threat level and block access when risk is elevated.
What makes this powerful for financial institutions: every compliance check generates an auditable record. When an NCUA examiner asks how you manage endpoints, you can pull a report showing encryption status, OS versions, and compliance rates across your entire fleet.
How Does Your Endpoint Security Stack Up?
ABT's free Security Grade Assessment measures your Microsoft 365 environment against the device compliance standards regulators expect. Get a scored report in minutes, not weeks.
Building a Risk-Based Intune Policy: The Executive Playbook
A one-size-fits-all compliance policy creates problems. A branch teller's workstation has different risk characteristics than a loan officer's personal phone. A risk-based approach treats devices differently based on what they access and the threat they represent.
Step 1: Define Your Compliance Baseline
Start with the minimum standard every device must meet before touching corporate data. For most financial institutions, that baseline includes BitLocker encryption on Windows devices, a minimum OS version no more than one major release behind current, a device PIN or biometric, and active antivirus with cloud-delivered protection enabled.
A mortgage company processing loan applications and a community bank running hybrid branch operations will both need these minimums. The details differ by platform (separate policies for Windows, iOS, Android, and macOS), but the principle holds.
Step 2: Configure Policies and Non-Compliance Actions
In the Intune admin center, you create compliance policies per platform. The critical decision: what happens when a device fails?
Options range from sending the user a notification email to immediately marking the device non-compliant. For regulated organizations, most compliance frameworks expect prompt flagging rather than a week-long grace period. A credit union with 300 employees might allow 24 hours for an OS update before blocking access. A bank processing wire transfers might allow zero grace period for missing encryption.
The FFIEC Information Security Booklet requires institutions to manage all data exit points, including removable media and portable devices. OCC Bulletin 2023-22 specifically evaluates processes to manage removable media and portable devices, alongside data disposal and device sanitization procedures. Examiners expect documented policies, automated enforcement, and auditable evidence. If your compliance policies exist only in a Word document and not as automated Intune rules, the examiner will note the gap.
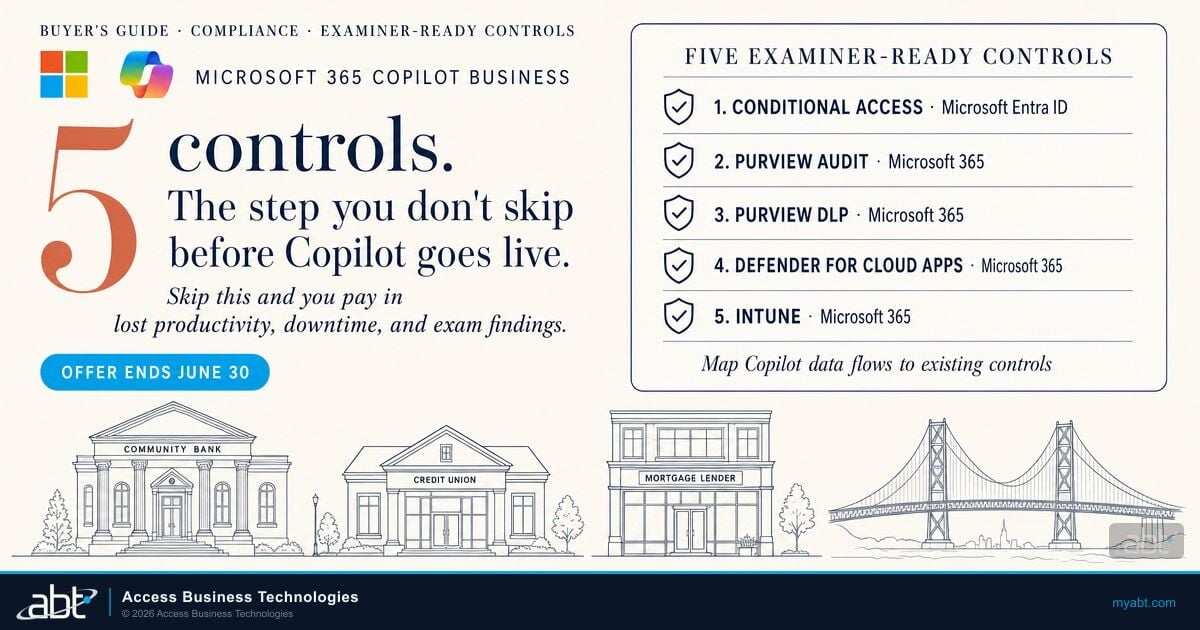
Step 3: Enforce Through Conditional Access
A compliance policy alone just checks devices. Intune Conditional Access is the enforcement mechanism that acts on those checks. You create a Conditional Access rule that states: if a device is non-compliant, block access to Microsoft 365 resources.
This creates a closed loop. Intune flags a device. Conditional Access blocks that specific device. The user's other compliant devices keep working. The loan officer whose laptop missed a security update loses access on that one machine until the update installs. No phone calls to IT. No tickets. The system handles it. For a deeper look at how these policies work together, see our guide on Conditional Access rules every financial institution needs.
Step 4: Test in Report-Only Mode Before Enforcement
Deploy Conditional Access policies in "Report-Only" mode first. This shows you who would be blocked without actually stopping anyone from working. A credit union running this pilot might discover 40 devices on outdated OS versions that need attention before going live. A mortgage company might find that half their loan officers are using personal tablets that haven't been enrolled.
Two weeks of report-only data prevents the "scream test" where you flip a switch and immediately lock out half the organization.
What Changed in 2026: Intune's Expanding Capabilities
Microsoft is making significant investments in Intune that directly benefit financial institutions on E3 and E5 licenses:
- Advanced Analytics: AI-powered anomaly detection that proactively identifies device health issues. Instead of waiting for a compliance failure, Intune surfaces emerging problems before they trigger an incident. For a CISO managing hundreds of endpoints, this shifts the posture from reactive to proactive.
- Endpoint Privilege Management: Allows organizations to adopt least-privilege access at the device level. Users get elevated access only for approved applications, with just-in-time elevation that maintains productivity without granting standing admin rights. This directly addresses the regulatory expectation for least-privilege controls. Copilot in Intune now provides risk assessments based on Defender threat intelligence before IT approves an elevation request.
- Cloud PKI: Certificate-based authentication managed entirely from the cloud. No on-premises infrastructure required. For financial institutions still running hybrid environments, this simplifies a historically painful deployment. Microsoft says setup takes minutes instead of weeks.
- Android Strong Integrity enforcement: Intune now enforces Google's updated "Strong Integrity" definition for Android 13+ devices, requiring hardware-backed security signals. A device that can't prove its integrity at the hardware level gets blocked.
These additions reinforce a trend: Microsoft is building Intune into a comprehensive endpoint security platform, not just a device management tool. Gartner predicted that by 2025 more than 90 percent of enterprises would use cloud-based unified endpoint management tools, up from 50 percent in 2022. Intune is positioned as the default for organizations already inside the Microsoft ecosystem.
The Microsoft 365 Security Ecosystem: Intune Doesn't Work Alone
One of the most common mistakes financial institutions make: buying Microsoft 365 for email and ignoring the security engine underneath.
Intune is one piece of an integrated ecosystem:
- Microsoft Defender for Endpoint feeds threat intelligence into Intune compliance policies. A device with an active threat gets flagged non-compliant automatically.
- Microsoft Entra ID uses Intune's compliance signals to make Conditional Access decisions. Identity verification and device posture work together. We explore this identity-device relationship in depth in our article on how Conditional Access turns device signals into real-time access decisions.
- Microsoft Purview enforces data protection policies that Intune helps deliver to endpoints. Sensitive borrower data stays inside approved applications.
When you treat Microsoft 365 as a platform rather than a collection of apps, you eliminate the need for separate MDM, antivirus, and encryption vendors. That consolidation reduces vendor complexity and IT spend, a direct ROI for CFOs watching the budget. For a full breakdown of how this platform approach works, see our guide to Microsoft 365 compliance for GLBA and OCC requirements.
Implementation Realities: What Financial Institutions Actually Face
Deploying device compliance policies isn't without friction. The three challenges that surface in nearly every engagement:
BYOD pushback. Loan officers and field staff resist having "company management" on personal phones. The distinction between MAM (which protects company data) and MDM (which manages the whole device) matters here. Clear communication that MAM can wipe company emails without touching personal photos defuses most resistance. For mortgage companies where loan officers live on personal devices, leading with MAM before MDM is usually the right sequence.
Configuration complexity. Intune has thousands of settings. A misconfigured policy at a credit union could lock tellers out of their core banking application mid-transaction. A policy that's too permissive at a bank might satisfy no one when the FFIEC examiner arrives. Getting the configuration right requires knowing both the technology and the regulatory expectations.
Ongoing maintenance. Compliance isn't a one-time deployment. OS versions change, new threats emerge, Microsoft updates its platform, and policies need regular tuning. A policy you set correctly six months ago may have gaps today.
"The attack surface has expanded with the evolution of new technologies and broadly-used remote access points, including mobile computing, smartphone applications, bring your own devices, and cellular connections."
FFIEC Authentication and Access GuidanceWhy Professional Implementation Changes the Equation
Microsoft provides the tools. Configuring them for a regulated financial institution requires a different level of expertise.
ABT's Guardian operating model takes the foundation of Microsoft 365 Business Premium and layers on hardening purpose-built for financial services endpoint security. As a Tier-1 Cloud Solution Provider serving 750+ financial institutions, ABT handles Intune device compliance configuration, Conditional Access integration, and ongoing policy management.
The Guardian lifecycle covers what matters:
- Hardening: Compliance policies, encryption enforcement, and Conditional Access rules configured correctly from day one.
- Monitoring: Continuous compliance drift detection. When a device falls out of compliance, you know immediately.
- Insights: Reporting that maps directly to examiner expectations from NCUA, OCC, FFIEC, and state regulators.
- Response: When an incident occurs, ABT has the tools and automation to revoke access, isolate the device, and contain the threat.
Whether you're a credit union preparing for an NCUA exam, a mortgage company meeting state licensing requirements, or a community bank responding to OCC guidance, Guardian closes the gap between "licensed" and "secured."
The Bottom Line for Financial Institution Leaders
Every unmanaged device accessing your Microsoft 365 environment is a risk you can measure. Intune device compliance policies turn that risk into a controlled, auditable process. The tools are already in your Microsoft license. The question is whether they're configured to meet the standards your regulators, insurers, and board expect.
Stop guessing about your endpoint posture. Start enforcing it.
Your Regulators Will Ask About Device Compliance. Have the Answer Ready.
ABT configures Intune compliance policies, Conditional Access enforcement, and endpoint monitoring for banks, credit unions, and mortgage companies. One conversation shows you the gap between your current posture and what examiners expect.
Frequently Asked Questions
No. When using Mobile Application Management or BYOD enrollment, Intune isolates business data from personal data on the device. IT administrators can wipe company emails and files if an employee leaves, but they cannot access personal text messages, photos, or browsing history. This separation is a core design principle of the platform.
The response depends on your policy configuration. Typically the device receives a short grace period to resolve the issue, such as installing a required OS update. If the device remains non-compliant after the grace period, Conditional Access blocks it from accessing Microsoft 365 resources like Teams, SharePoint, and OneDrive until remediation is complete.
Yes. Intune is included in Microsoft 365 Business Premium and Enterprise E3 and E5 plans. Starting July 2026, Microsoft is expanding Intune Suite capabilities in E3 and E5 to include Advanced Analytics, Endpoint Privilege Management, and Cloud PKI at no additional cost, giving financial institutions more security tools without new licenses.
Intune generates documented compliance reports showing encryption status, OS versions, and device health across your entire fleet. These reports provide the audit-ready evidence that NCUA, OCC, FFIEC, and state examiners expect when they ask how your institution manages endpoint security. Policies are enforceable and logged, not just written on paper.
Yes. Intune supports full device enrollment with MDM for company-owned hardware and lighter MAM-only policies for personal devices. This dual approach lets financial institutions enforce strict compliance on corporate laptops and workstations while protecting business data on personal phones without overreaching into employee privacy.

Justin Kirsch
CEO, Access Business Technologies
Justin Kirsch has led endpoint security deployments at hundreds of financial institutions as CEO of Access Business Technologies. His team manages Microsoft Intune configurations across banks, credit unions, and mortgage companies where device compliance directly determines regulatory examination outcomes. He writes about translating Microsoft's enterprise security tools into practical frameworks for the financial services sector.